For several years now, various security companies have been reporting on the threat from North Korean operatives linked to the Democratic People's Republic of Korea posing as remote developers, engineers, and contractors to gain employment at foreign companies, particularly in tech. Once inside, they generate revenue for the regime, exfiltrate sensitive data, and in some cases enable follow-on cyber operations or extortion schemes. These campaigns have made front page news, but that hasn’t slowed down in 2026
Augur has been tracking & protecting against the North Korean threat cluster that includes Temp.Hermit, UNC2970, LazarusGroup since early 2017. To counter this threat, advanced background checks are not enough. Augur’s Preemptive cyber intelligence can prevent fraudulent threat actors from joining your team and significantly degrade the toolset they use once they’ve joined.
1. Context
This report analyzes a high-velocity offensive originating from the Democratic People’s Republic of Korea (DPRK) throughout 2025 and early 2026. This threat cluster is characterized by a "decentralized threat" model, where multiple independent teams operate in parallel under the broad sponsorship of the Reconnaissance General Bureau (RGB), the DPRK’s primary department for military intelligence and clandestine operations. Attribution in this space is complicated by shared tradecraft; different teams using the same malware families and infrastructure providers while maintaining distinct targets and operational objectives. This allows threat actors to quietly reach operational objectives while muddying evidence that would lead to identification and attribution.
The current threat landscape is defined by three primary workstreams: Contagious Interview, Fake IT Worker operations, and the March 2026 Stegabin campaign. These campaigns prey on the global shift toward remote work to infiltrate high-value tech and finance sectors. By masquerading as software engineers and help desk staff, North Korean actors like UNC2970 and Lazarus have successfully been able to steal over $2 billion from crypto firms and enterprise victims alike.
1.1 The Challenge of Attribution
Industry research often tracks this activity under a variety of monikers, like Temp.Hermit, UNC2970, or the infamous LazarusGroup because operational reality is a mosaic of subgroups. These teams exhibit varying levels of technical proficiency, with some operators manually fixing code errors in real time while others rely heavily on AI-driven coding and obfuscation.
Evidence from GitLab’s exposé into private projects suggests these teams often overlap in time and target space but show limited evidence of centralized command for tactical decisions. Instead, they appear to be independent cells (such as the Kil-Nam Kang cell in Beijing or the Moscow-based IT worker groups) tasked with quarterly quotas for revenue and intelligence, free to develop their own localized personas and infrastructure.
1.2 The Strategic Landscape
The North Korean cyber doctrine in 2026 revolves around three core pillars:
- The Weaponization of Professional Trust: Threat actors identify software engineers on platforms like LinkedIn and GitHub to initiate " technical interviews." During these interactions, they induce the target to download and execute malicious code repositories under the guise of a coding challenge.
- State-Sanctioned Employment Fraud: Thousands of North Korean nationals are currently operating under stolen or synthetic identities to gain legitimate employment at Western technology firms. These workers ignore simple data theft and generate a steady stream of hard currency and lateral access to internal corporate environments for future operations.
- The Laptop Farm Infrastructure: To bypass modern geolocation and identity verification, these actors have established a sophisticated network of local facilitators in the U.S. and Europe. These facilitators host physical hardware that the North Korean operators access remotely, effectively masking their true origin and bypassing IP-based security controls.
Augur Security confirms that these are no longer siloed efforts. The personal data and corporate credentials stolen during "Contagious Interview" strikes are directly fed into the "Fake IT Worker" pipeline to build more authentic personas. These personas, with their credible online backgrounds, then release malicious projects and poisoned packages back into their network, creating a self-sustaining cycle of infiltration and theft.
2. North Korean Threat Clusters and their Structure
In reality, these North Korean cyber cells function less like a military unit and more like a collection of specialized franchises. The RGB provides the initial funding while the strategic targeting and tactical execution are delegated to regional cells and their leaders. These cells operate with a high degree of autonomy, thus explaining the significant variance in technical skill and infrastructure quality observed across different campaigns. Workload distribution and segmentation also allows the regime to ensure that the compromise of a single cell does not expose the entire program.

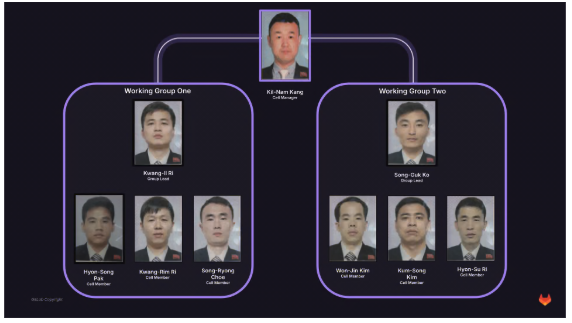
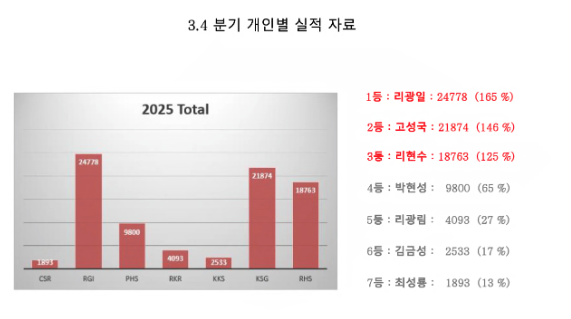
A primary example of this corporate-style logic is the Beijing-based cell managed by Kil-Nam Kang (강길남), head of the China-based DPRK cell. Kang oversees a structured operation divided into two distinct working groups, as identified through leaked project records. This documents demonstrate a clear division of labor:
- Management Tier: Kil-Nam Kang serves as the Cell Manager, coordinating the activities of two sub-teams to meet revenue and intelligence quotas.
- Working Group One: Led by Kwang-Il Ri, this group includes members Hyon-Song Pak, Kwang-Rim Ri, and Song-Ryong Choe.
- Working Group Two: Led by Song-Guk Ko, this group consists of Won-Jin Kim, Kum-Song Kim, and Hyon-Su Ri.
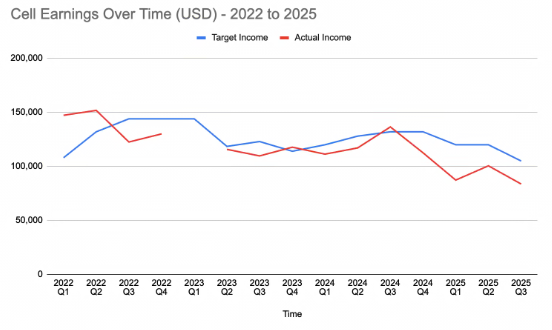
Records recovered from this cell indicate an eight-person team that generated over $1.6 million in revenue through freelance development while simultaneously maintaining dossiers on foreign facilitators. These cells balance critically important responsibilities, as they must act as both profit centers and intelligence gatherers.
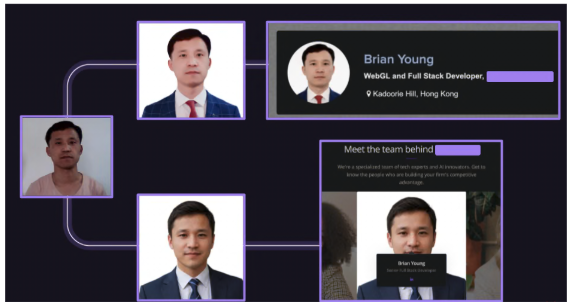
Historically, the Beijing cell has focused on revenue and facilitator management; a separate cluster operating out of Moscow prioritizes the technical front-end of the operation. These teams specialize in the backstopping of identities, using AI headshot services and stolen U.S. documents to create professional personas that appear legitimate to Western HR departments. These actors also leverage Russian infrastructure to add a layer of geographic obfuscation, complicating traditional attribution.
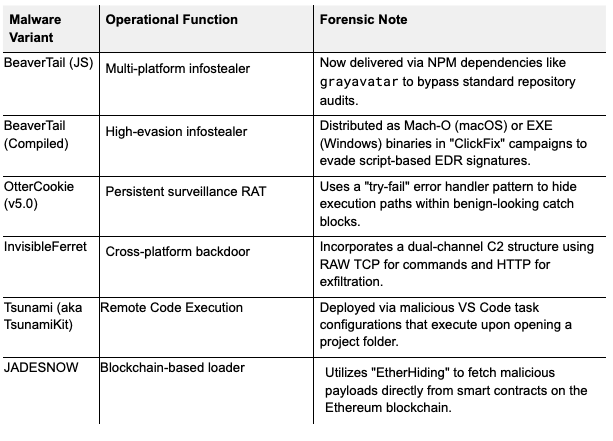
The connective tissue between these dispersed clusters is a shared pool of resources rather than a direct command-and-control structure. These franchises pull from a central shared library of malware, such as the BeaverTail and Ottercookie repositories, but customize delivery methods to suit their current needs. This allows the RGB to guarantee a baseline of technical capability across all cells while preserving the freedom of individual cells to pivot independently when needed. The result is a compartmentalized series of campaigns, where a failure in Beijing has no technical impact on operations in Moscow; cells continue operations unaffected.
3. Operational Details
The operational lifecycle of the North Korean 2026 offensive concentrates on targeted social engineering. Unlike traditional groups that favor broad phishing blasts, these cells employ a months-long strategy that prioritizes access quality over target volume.
3.1 The Contagious Interview
The attack typically begins on professional networking platforms where actors pose as recruiters for high-growth tech or crypto firms. The engagement follows a specific sequence:
- The Bait: A "recruiter" contacts a developer about a lucrative role, often moving the conversation to Telegram or Discord to bypass platform monitoring.
- The Technical Challenge: The target is invited to a technical interview that requires them to clone a GitHub or GitLab repository to complete a "coding test."
- Execution: These repositories contain the BeaverTail stealer hidden within legitimate-looking JavaScript dependencies. Once the developer runs the project locally to "test" their code, the malware executes, exfiltrating browser data, passwords, and cryptocurrency wallet keys back to the cell's C2 infrastructure.
3.2 The Fake IT Worker (WageMole) Strategy
Simultaneous to the malware strikes, the groups use their cultivated personas to apply for legitimate remote positions. The GitLab intelligence revealed that this is not a side-hustle but a genuine means of revenue generation for independent cells.
- Personas and AI: In the Moscow cluster, actors use AI to polish stolen identities, ensuring their LinkedIn profiles and video interview appearances withstand standard HR scrutiny.
- The Laptop Farm: To maintain the illusion of being local, workers recruit "facilitators" in the U.S. and Europe to host physical laptops. The North Korean worker remotes into this hardware, ensuring their IP address always maps to a trusted home or office location.
- Dual Mission: Once hired, these workers fulfill their daily job requirements to collect a salary, while simultaneously probing internal corporate networks for lateral movement opportunities. This creates a "warm" persistence that traditional firewalls cannot detect.
3.3 The StegaBin Campaign
Augur’s tracking of the March 2, 2026, StegaBin campaign reveals significant professionalization in the infrastructure resolution tactics used by the Famous Chollima cluster. North Korean actors have long viewed the npm registry as a primary delivery vector, but StegaBin introduces a layer of obfuscation designed to survive deep manual audits. Threat actors were able to publish 26 malicious packages (like argonist, bcryptance, and vitetest-lint), giving operators numerous, invisible footholds in the victims’ environment.
- Steganographic dead drops were utilized heavily. The malware avoids hardcoded C2 strings by utilizing a multi-stage steganographic decoder. It fetches seemingly benign computer science essays from Pastebin, where a custom script reconstructs hidden C2 addresses by extracting characters at specific, evenly spaced intervals. This dead-drop technique currently leverages 31 Vercel deployments, allowing the adversary to hide operational logic within benign prose and bypass automated string-based detection.
- The payload weaponizes the legitimate TruffleHog scanner to automate the identification and theft of private keys and hardcoded credentials within local repositories. In addition to the exfiltration of macOS iCloud Keychains and browser data, this collection suite provides the unrestricted access necessary to pivot from a single compromised workstation to a full-scale corporate breach.
3.4 Integration into the Broader DPRK Ecosystem
These localized activities do not exist in a vacuum. DPRK cyber operations and their independent cells serve as the primary feed for the broader North Korean financial and intelligence ecosystem. The credentials and cookies harvested during Contagious Interview campaigns are frequently recycled for separate operations targeting large-scale decentralized finance (DeFi) heists. The sensitive corporate data obtained by North Korean IT workers (internal Slack logs, executive resumes, and source code) is later leveraged to create even more authentic personas for future infiltrations.
This creates a self-reinforcing cycle where stolen data from one company is used to bypass the identity verification of another. The revenue generated, such as the $1.64 million recorded by the Kil-Nam Kang cell, is often laundered through complex chains of cryptocurrency mixers before being diverted to the regime’s weapons programs. Additional liaising with broader state-sponsored groups like Lazarus allows these smaller cells to ensure that every piece of exfiltrated data is monetized, whether through salary, identity fraud, or strategic corporate espionage.
AI Enhanced Development
Another significant shift in 2026 is the role of Artificial Intelligence in the development cycle. Actors have now gone beyond using AI for simple social engineering lures and are now using it as a quality-assurance and obfuscation engine.
- Adversarial Obfuscation: Threat actors provide their source code to LLMs and task them with creating custom obfuscators. They then use the AI to attempt to "solve" or de-obfuscate the result. If the AI can decode it, the actor iterates on the code until it reaches a level of complexity that bypasses automated de-obfuscation tools.
- Standardization: AI allows decentralized cells to produce standardized, high-quality code that mimics professional enterprise software, making it harder for analysts to find amateur coding mistakes that previously led to attribution.
4.3 Astrill VPN Abuse
Forensic telemetry from the 2025 Operation Phantom Circuit and the subsequent 2026 GitLab disruption confirms that Astrill VPN serves as the primary logistical bridge for North Korean cells operating out of Chinese villas in Dalian and Shenyang, as well as safe houses in Vladivostok and Moscow. The service is uniquely suited to the regime’s requirements due to its StealthVPN and Router VPN protocols, which are famously resilient against the Great Firewall, providing the high-bandwidth stability necessary for live technical interviews and sustained corporate access. Beyond simple connectivity, Astrill is leveraged for its private IP options, which allow fake IT workers to maintain a consistent geographic footprint. This is a critical defensive bypass as appearing to log in from the same fixed location daily permits operators to avoid triggering "impossible travel" alerts in corporate Slack or HR environments. Even the service’s branding, a star inside a circle, serves as a piece of symbolic tradecraft, mirroring the star on the DPRK flag and attracting operators as a preferred utility for state-backed campaigns (a fact which Astrill employees themselves have acknowledged).
The regime weaves Astrill directly into its identity factory and malware delivery lifecycle. Before an operator initiates contact with a victim, they perform weeks of persona warming, maintaining active Astrill sessions to build a geographic history for the persona’s cookies and browser fingerprints across LinkedIn and GitHub. Operation Phantom Circuit revealed that Lazarus subgroups further utilize Astrill exit points to manage command-and-control servers, routing administrative RDP and SSH traffic through the VPN to mask the manager’s safe house. This infrastructure also facilitates the test-firing of new BeaverTail or OtterCookie payloads, where developers use Astrill IPs to validate malware handshakes against decoy targets before full-scale deployment. The VPN also has built-in tools supporting a staged data theft strategy, allowing source code or crypto seed phrases to be trickled out over several days to mimic legitimate git-push traffic and evade data-loss prevention triggers.
However, this reliance on a centralized service creates a significant operational vulnerability through human-layer OPSEC failures. Despite the VPN’s closed-loop, the biggest weakness remains the kill-switch failure. There are documented forensic instances where an Astrill client crash exposed the operator’s true fixed-line IP from TransTelekom in Russia or China Unicom, momentarily exposing the operator and creating a bridge from a domestic US persona to a state-sponsored safe house. Furthermore, operators frequently make dual-login mistakes (where lazy operators reuse the same private IP to manage multiple personas across different victim organizations), allowing researchers to link seemingly independent contractors back to the same DPRK cell. Monitoring for these specific exit node signatures and handshake patterns allows security teams to disrupt the entire operational tunnel. Alongside advanced infrastructure identification and preemptive blocking, teams can even force the adversary to abandon warmed identities and restart their staging process.
5. Victimology and Targeting
Augur Security and GitLab’s telemetry confirm that North Korean operations have moved away from broad, indiscriminate phishing toward a highly surgical targeting model. By 2026, the primary objective is no longer just securing corporate access, but specifically identifying individuals who hold powerful credentials. This ranges from software engineers, IT administrators, and high-net-worth executives in the decentralized finance (DeFi) space to low-level help desk staff at Fortune 500 companies.
5.1 Targeting Psychology and the Contagious Interview
The targeting methodology relies on long-term social engineering rather than immediate technical exploitation. Actors prioritize the quality of rapport over the quantity of outreach. They often spend several weeks interacting with a target to normalize the eventual request for local code execution.
- Sector Prioritization: Threat actors focus on decentralized finance and artificial intelligence sectors. These industries offer high liquid assets and a workforce accustomed to executing unverified code for technical assessments.
- The Recruiting Lure: Operatives impersonate recruiters from legitimate high-growth startups. They use professional networking platforms to identify individuals with access to private repositories or production environments.
- Platform Transitioning: To avoid detection by security algorithms on sites like LinkedIn, the actors move the engagement to encrypted channels such as Telegram or Discord. This transition creates a false sense of exclusivity and privacy for the victim.
- The Technical Screen: The victim is induced to download a malicious coding challenge. This lure bypasses traditional network edge security because the victim willingly pulls the repository onto their local workstation.
- ClickFix Evolution: Recent campaigns utilize the ClickFix technique. Victims visit a fake interview portal where a simulated camera error prompts them to run a fix script. This script executes the BeaverTail payload while the victim believes they are simply troubleshooting their browser for the meeting.
The Fake IT Worker: Strategic Insider Infiltration
Beyond malware strikes, the regime utilizes fraudulent employment to gain authorized, persistent access to Western corporate systems. This represents a strategic shift from external hacking to the cultivation of a state-sponsored insider threat.
- Identity Backstopping: North Korean workers utilize artificial intelligence to modify stolen identity documents and create credible professional personas. They maintain verified profiles that withstand standard human resources scrutiny.
- Infrastructure Obfuscation: To bypass geolocation alerts, these actors utilize laptop farms located within the United States and Europe. Local facilitators host physical hardware, which the North Korean operator accesses remotely to maintain a trusted domestic IP address.
- Privileged Escalation: Once hired, these workers do not immediately steal data. They act as model employees for months while slowly accumulating access to internal VPNs (like Astrill), source code repositories, and Slack channels. This insider status allows them to exfiltrate proprietary data or plant backdoors that appear as routine administrative changes.
5.2 Record-Breaking Gains: 2025 Through Early 2026
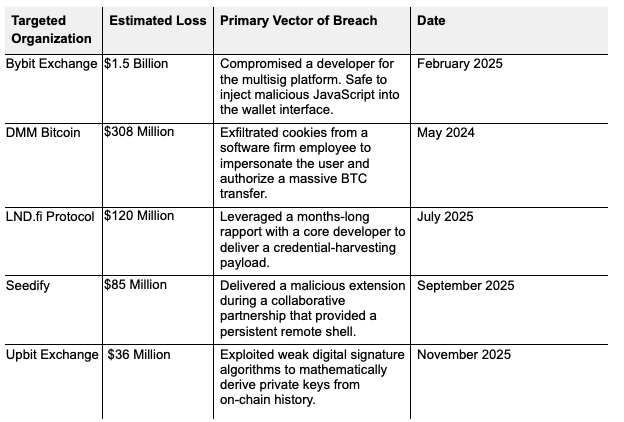
The North Korean regime achieved its highest recorded theft value in 2025. Data indicates a shift toward fewer but significantly larger heists. The ratio between the largest hack and the median incident has crossed the 1,000x threshold for the first time, confirming the subtle shift in North Korean threat posture. Instead of leveraging simple backdoors, the threat cluster has pivoted to Interface Subversion. In the Bybit and DMM Bitcoin cases, the actors did not exploit the blockchain directly but instead compromised the human-facing software, demonstrating that even the most robust cryptographic security can fail when the human layer is successfully deceived.
6. The Gitlab Leaks
Augur’s advanced modeling was validated by the 2026 disruption of private North Korean repositories on GitLab, an event that gave Augur analysts a deep look inside the sprawling bureaucracy governing these operations. The leaked data confirms that these campaigns are not the output of disparate threat actors but are state-backed units operating with a degree of corporate rigor that rivals Western software firms. This environment is defined by structured performance reviews, aggressive financial quotas, and high-stakes personnel logistics aimed at maintaining a permanent presence in the global economy.
6.1 The Bureaucracy of Cyber Theft
A centralized management layer bridges the gap between the regime’s strategic requirements and the tactical output of individual operators. The discovery of private ledgers belonging to Kil-Nam Kang, a North Korean intelligence official who served as a handler and project manager, exposed a sophisticated tracking system in which every operative is managed as a revenue-generating asset. These handlers maintain dossiers on their subordinates that include passport copies, administrative credentials for remote workstations, and real-time tallies of daily campaign revenue. This system provides military command with absolute oversight of workers stationed at overseas hubs such as Beijing or Moscow, ensuring that operational security is maintained under a "Zero Trust" internal policy.
The financial viability of these micro-cells is substantial; a single eight-person unit generated over $1.64 million USD in earnings over a three-year period. This was achieved through a hybrid model that fused legitimate freelance software development with targeted malware distribution. By maintaining this dual-revenue stream, the cell maintains a pipeline within the Western tech ecosystem, cultivating professional reputations that serve as the fundamental trust layer for more destructive "Contagious Interview" operations.
6.2 The Identity Factory and Synthetic Legitimacy
The 2026 reporting reveals a pivot toward industrial-scale identity synthesis. The regime has moved beyond simple social engineering into a factory-like system of "synthetic backstopping,” a process that creates deeply documented personas with verified professional histories and automated social connections. These identities are "warmed up" over months of AI-driven activity, making them virtually indistinguishable from legitimate industry peers by the time they contact a high-value target.
GitLab artifacts further highlight a transition in identity maintenance. Operators utilize AI-headshot services to transform original photos (captured in safe houses in Moscow or China) into professional, high-fidelity LinkedIn portraits. These synthetic personas are leveraged to recruit "facilitators" in the U.S. and U.K. who unknowingly provide the physical infrastructure (known as residential "laptop farms") required for these attacks. This pipeline of human facilitators and AI-generated media creates a robust defensive barrier that neutralizes traditional HR and IT vetting, permitting threat actors to bypass the perimeter and begin infiltration from a trusted "internal" position.
6.3 Adversarial Innovation: AI as a Shield
Technical analysis of these repositories confirms that North Korean developers are weaponizing Large Language Models (LLMs) to refine their tradecraft beyond simple code generation. They use AI to audit their own obfuscation, test malicious payloads, and automate lateral-movement scripts. By posing as security researchers in prompts, developers trick LLMs into "stress testing" their malware and suggesting iterative improvements under the guise of academic research. This creates a highly effective quality-assurance layer, ensuring that JavaScript payloads such as BeaverTail are optimized to evade the de-obfuscation heuristics of modern EDR platforms.
This cycle of continuous improvement has fundamentally altered delivery mechanisms. The current operational baseline involves "silent" triggers within development environments. By embedding malicious logic in VS Code task files and masquerading payloads as benign font assets or software supply packages, actors ensure that malware executes the moment a victim opens a project folder. This seamless technical "flow" minimizes the number of user-initiated actions required for infection, directly contributing to the 9% success rate currently documented in their master target dossiers.
6.4 Augur Takeaway
The connective tissue revealed through the GitLab disruption proves that the North Korean threat is defined more by "process" than by "malware." The regime has built a global, resilient, and highly profitable engine that exploits the inherent trust within the global developer community. They have turned the professional interview process into an attack vector and transformed legitimate software development tools into a delivery system for credential theft and supply chain attacks. As we transition into the technical indicators, the focus must remain on the fact that every hash and IP address in this report is a tool of a professionalized state bureaucracy working under a strict, military-enforced quota. To ensure your organization is protected, attacker infrastructure must be blocked alongside malicious indicators, preventing campaign operations from ever reaching command-and-control platforms.
7. Technical Indicators
The following Indicators of Compromise (IOCs) represent a snapshot of the infrastructure currently tracked by Augur as part of this threat cluster, specifically the "Contagious Interview" and "Fake IT Worker" threat cluster. Unlike traditional attacks that rely on sudden bursts of activity, these indicators represent a "low-and-slow" staging process. Augur identifies these assets an average of 51 days before the first outreach is made, providing a critical window for preemptive blocking. In the 2026 landscape, the distinction between state-sponsored espionage and financially motivated crime has functionally dissolved. Augur advises security teams to treat any interaction with these indicators as a high-fidelity signal of imminent or active targeting.
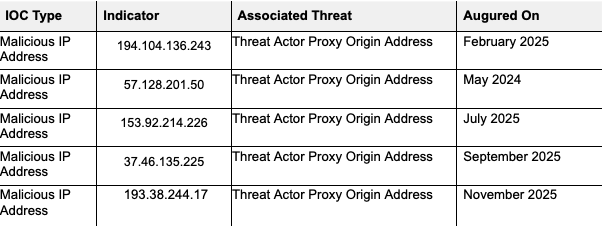
The 2026 data shows that the DPRK threat cluster relies heavily on a network of third-party facilitators to bridge the gap between their operators (physically located in China or Russia) and their targets in the West. This infrastructure is designed to defeat geolocation and identity verification by combining physical hardware and residential proxying.
- Facilitated Hardware (Laptop Farms): A major component of this cluster is the use of laptop farms; physical devices hosted by facilitators in the U.S. and U.K. to provide a domestic IP address for the remote worker. Recent law enforcement actions against facilitators like Oleksandr Didenko (sentenced in February 2026) have exposed threat actor reliance on sites like Upworksell.com to manage thousands of stolen identities and physical hardware nodes.
- Residential Proxy Overlap: To further mask their origin, these actors use residential proxy services that rotate through legitimate home IP addresses, making traditional IP blocking difficult, as the actors' traffic appears to originate from the same neighborhood as a company's actual employees.
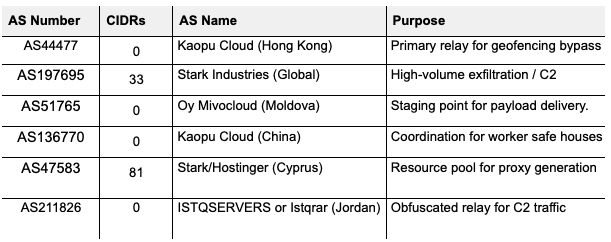
Despite threat actors' attempts to mask their infrastructure, their backend management and C2 (Command and Control) traffic frequently traverse specific, high-risk ASNs known to host DPRK-linked assets. The CIDR counts below reflect the specific segments within these networks that exhibit the malicious behavioral patterns (such as silent registration and proxy-chaining) associated with this cluster.
8. Recommendations for CISOs
The 2026 North Korean threat landscape marks a definitive end to the era of purely technical perimeter defense. Augur Security’s predictive intelligence, alongside forensic data from GitLab, confirms that North Korean operations have reached a level of maturity where traditional EDR is merely a burden. Instead, the human vetting process is their target for subversion. The North Korean regime’s pivot toward high-rapport social engineering and the deployment of synthetic identities requires a transition from reactive malware detection to a preemptive, architectural posture that neutralizes malicious intent before the first line of code is ever executed.
8.1 Preemptive Infrastructure Blocking with Augur
The most effective way to disrupt these campaigns is to neutralize adversary infrastructure during the staging phase. Augur Security provides the capability to move beyond signature-based detection by identifying the telltale patterns of global internet telemetry that signal the setup of a command-and-control (C2) environment.
- Predictive Asset Identification: By analyzing the setup of Virtual Private Servers and ephemeral proxies on high-risk networks like Stark Industries or Kaopu Cloud, Augur can block the Tier 1 nodes North Korean actors use for C2 communication at the network layer. Blocking these assets at the network layer before the BeaverTail or OtterCookie payloads are deployed breaks the malware execution chain at its most vulnerable point, before they gain a foothold in your environment.
- Malicious Registry Monitoring: Proactive defense requires constant surveillance of the NPM and PyPI registries for typosquatting and brandjacking. Augur enables organizations to flag and block connections to domains associated with malicious package metadata, preventing developers from unknowingly pulling poisoned dependencies (such as node-nvm-ssh) during technical assessments.
- Geofencing and ASN Reputation: CISOs should implement aggressive blocking of Autonomous System Numbers (ASNs) frequently abused by DPRK cells for laptop farms and remote bypass. This measure ensures that even if a fraudulent worker bypasses HR screening, their remote-access hardware (IP-based KVMs or RMM tools) cannot establish a persistent connection to the corporate VPN.
8.2 Architectural Hardening and Behavioral Guardrails
Neutralizing the Contagious Interview cycle requires structural changes to how technical teams interact with external parties. The objective is to remove the local developer workstation from the attack surface entirely, treating every external project as a potential attack surface.
- Virtual Interview Environments: Organizations must mandate that all technical assessments be conducted in isolated, cloud-based IDEs. This prevents the execution of malicious VS Code tasks or NPM packages on employee hardware and ensures that any BeaverTail infection remains contained within a disposable sandbox.
- Phishing-Resistant Identity (FIDO2): Implementation of FIDO2-compliant hardware keys is the only reliable defense against the session hijacking and cookie-theft tactics seen in the Bybit and DMM Bitcoin heists. Moving away from SMS or app-based MFA remains the only way security leaders targeted by North Korean threat actors can remain secure, as even if an actor steals a credential, they lack the physical "possession" factor required to authenticate.
- Vigilant Remote Onboarding: Behavioral monitoring must focus on the use of unauthorized remote-management tools like AnyDesk or SimpleHelp. Establishing a strict whitelist of allowed administrative software allows the SOC to treat any unauthorized remote access binary as a high-priority indicator of a state-sponsored insider. Additionally, CISOs should mandate a physical serial-number verification of laptops at onboarding and deploy automated "mouse jiggler" detection to identify facilitators masking the true location of a remote worker.
8.3 Wrap Up
Success in the 2026 environment depends on a CISO’s ability to recognize that identity is the new perimeter. Protecting the enterprise now requires verifying not just the credentials being presented, but the physical location, behavioral patterns, and hardware legitimacy of the user. By leveraging preemptive cybersecurity tools like Augur to block infrastructure at its point of creation, organizations can force the adversary to restart their staging process, significantly increasing their operational costs and reducing the window of opportunity for exfiltration, all before they breach your perimeter.
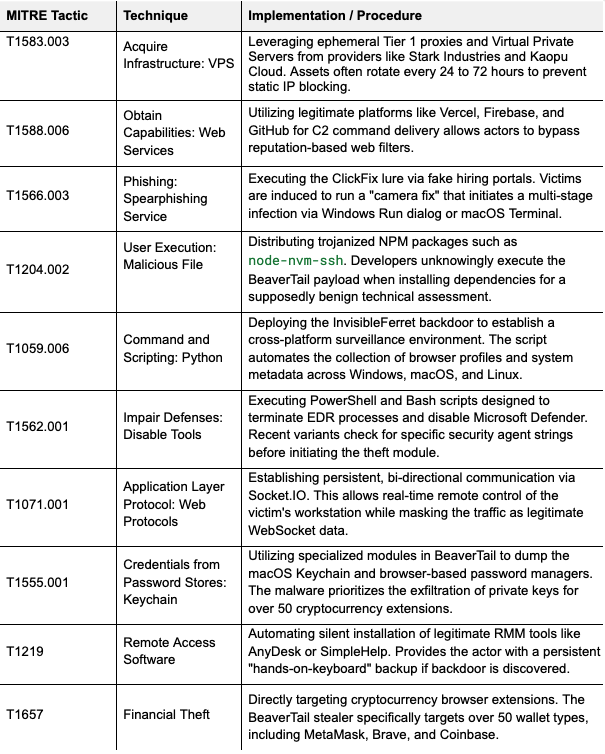
9. Key TTPs
10. References
[1] GitLab Threat Intelligence Team reveals North Korean tradecraft
[2] DPRK Linked Operators Sustain Aggressive Crypto Targeting 12 Months After Bybit Breach
[3] Google Reports State-Backed Hackers Using Gemini AI for Recon and Attack Support
[4] North Korea-Linked UNC1069 Uses AI Lures to Attack Cryptocurrency Organizations
[5] North Korean Hackers Publish 26 npm Packages Hiding Pastebin C2 for Cross-Platform RAT
Report prepared by Augur Research
For questions or additional analysis, contact: research@augursecurity.com