Executive Summary
As Content Delivery Networks (CDNs) underpin critical business services, they are increasingly exploited by AI-powered threat actors who use automation to rapidly scale phishing, malware delivery, and command-and-control activity while hiding inside trusted infrastructure.
This acceleration makes traditional reactive controls, such as blanket CDN IP blocking, both ineffective and disruptive, breaking essential SaaS and cloud applications while providing little lasting security value. Instead, organizations need a preemptive cybersecurity approach that focuses on identifying malicious behavior and infrastructure before attacks reach users.
How Augur Preemptive Cybersecurity Can Help
By continuously tracking CDN abuse, mapping threat actor infrastructure, and enabling selective monitoring rather than broad blocking, Augur helps security teams stay ahead of AI-driven campaigns, reduce operational risk, and defend the business without sacrificing availability or performance.
1. Technical Overview: CDN Architecture and Functionality
1.1 Core Purpose and Operation
Content Delivery Networks are geographically distributed proxy server networks that optimize content delivery by minimizing the physical distance between users and content sources. CDNs operate through several key mechanisms:
CDNs deploy Point of Presence (PoP) servers globally, caching static content (images, CSS, JavaScript, videos) at edge locations. When users request content, the CDN routes traffic to the nearest edge server, thereby reducing latency and load on the origin server.
CDNs employ intelligent routing algorithms using:
- DNS-based routing (returning geographically optimal IP addresses)
- Anycast routing (multiple servers sharing a single IP address)
- Geographic load balancing based on real-time network conditions
CDNs provide traffic optimization:
- Protocol optimization (HTTP/2, HTTP/3/QUIC support)
- Compression and minification
- TCP connection pooling and reuse
- TLS termination at edge nodes
1.2 Security Services
Modern CDNs extend beyond content delivery to provide security functions:
- DDoS mitigation absorbs volumetric attacks through distributed infrastructure.
- Web application firewalls (WAF) filter malicious application-layer traffic.
- Bot management distinguishes legitimate from malicious automated traffic.
- Rate limiting prevents abuse and credential stuffing attacks.
2. Threat Actor Motivation: Why CDNs Are Attractive
2.1 Operational Advantages for Adversaries
Infrastructure Legitimacy and Trust: Threat actors leverage CDN reputation to bypass security controls. Organizations frequently allow CDN IP ranges to ensure business continuity, creating security blind spots. CDN domains benefit from established trust, as security solutions may not scrutinize traffic from Cloudflare or Akamai as aggressively as they do from unknown infrastructure.
Attribution Challenges: CDNs provide natural anonymization layers. Multiple customers share CDN IP addresses, complicating attribution and forensic analysis. Traditional IP-based blocking becomes ineffective when legitimate and malicious traffic originates from the same infrastructure.
CDN infrastructure offers threat actors the same availability and resilience benefits as legitimate users, including high availability with uptime guarantees, DDoS protection for their own malicious infrastructure, global distribution that ensures campaign resilience, and rapid content propagation across geographic regions. Many CDNs also provide cost efficiency for malicious campaigns, as free tiers such as Cloudflare’s free plan with unlimited bandwidth and free static hosting on platforms like GitHub Pages and GitLab Pages eliminate financial trails and reduce operational costs.
2.2 Tactical Use Cases
CDNs host phishing pages that mimic legitimate services. Cloudflare Workers and Pages enable rapid deployment of credential-harvesting sites. The shared infrastructure model means phishing domains resolve to trusted IP ranges, evading IP reputation filters.
Threat actors upload malicious payloads to CDN-enabled file-sharing services or utilize CDN caching to distribute malware. GitHub releases, GitLab repositories, and object storage services backed by CDNs become distribution vectors.
Modern malware uses CDN-fronted command and control (C2) channels, including domain fronting techniques (though these are increasingly blocked), WebSocket connections routed through CDN reverse proxies, DNS tunneling via CDN resolvers, and API-based C2 that leverages CDN edge functions.
Evasion and Anti-Analysis: CDNs enable geographic filtering, allowing malware to activate only in specific regions, thereby evading sandboxes in different locations. Time-based delivery can serve legitimate content to victims during analysis and malicious content to them.
3. Malicious Activity Observed Since January 2025
3.1 Notable Campaigns and Tactics (January 2025 - October 2025)
Based on recent threat intelligence reporting, several significant CDN abuse patterns have emerged:
Operation Beamglea (NPM/UNPKG Campaign)
Researchers identified 175 malicious npm packages with approximately 26,000 downloads used in credential phishing campaigns targeting more than 135 industrial, technology, and energy companies worldwide. These packages leveraged npm's registry and unpkg.com's CDN to host redirect scripts that routed victims to credential-harvesting pages. The attackers created a resilient phishing infrastructure costing nothing to host by publishing packages across multiple accounts and automating victim-specific HTML generation, leveraging trusted CDN services.
The technical methodology involved:
- Automated Python scripts generating packages named "redirect-[random]"
- JavaScript files hosted on unpkg.com CDN (e.g., unpkg.com/redirect-xs13nr@1.0.0/beamglea.js)
- HTML email attachments, loading scripts from the CDN to redirect to fake Microsoft login pages
- Victim email addresses embedded in URLs for pre-filled phishing forms
FatalRAT APAC Campaign
In February 2025, industrial organizations across the Asia-Pacific region were targeted through phishing attacks that delivered FatalRAT malware. The attackers utilized legitimate Chinese cloud CDN services, including myqcloud and Youdao Cloud Notes, as part of their attack infrastructure. The campaign employed sophisticated multi-stage payload-delivery frameworks and DLL side-loading techniques, with the malware performing 17 checks in virtual machine or sandbox environments before execution.
SERPENTINE#CLOUD (Cloudflare Tunnel Abuse)
Security researchers have identified a campaign abusing Cloudflare Tunnel to host initial payloads and stagers, enabling attackers to serve dynamic, ephemeral content on local machines exposed to the public internet via temporary trycloudflare.com subdomains, all within a trusted cloud network. This eliminated the need for attackers to register domains or rent VPS servers, making takedowns and attribution significantly more difficult. Trycloudflare.com domains, fronted by Cloudflare's global CDN, were protected by TLS certificates, helping the infrastructure blend with legitimate traffic.
The infection chain involved:
- Malicious .lnk files disguised as documents
- Obfuscated batch scripts and VBScript stages
- Python-based shellcode loaders executing Donut-packed payloads in memory
- WebDAV over SSL for encrypted payload delivery
Cloudflare Pages/Workers Phishing Surge
Fortra reported a 198% increase in phishing attacks on Cloudflare Pages between 2023 and mid-October 2024, rising from 460 incidents to 1,370 incidents, with projections suggesting a year-over-year increase of 257% by year-end. Cybercriminals abused Cloudflare Pages by hosting intermediary phishing pages that redirect victims to malicious sites, such as fake Microsoft Office 365 login pages.
ClickFix Campaign Infrastructure
Analysis from mid-July to August 2025 identified 13,695 unique ClickFix-associated domains, with Cloudflare as the most prevalent hosting provider, accounting for 24.4% (3,345) of detected malicious domains. The campaign abused legitimate or institutional domains, including academic and government resources, likely due to opportunistic compromises or poorly maintained DNS records.
CDN Cache Persistence Exploitation
Security researchers found that malicious npm packages removed from the registry (e.g., "standforusz") remained accessible via the jsDelivr CDN weeks later due to persistent edge caching, allowing attackers to exploit this "permanent cache," where payloads remain globally mirrored even after source takedown.
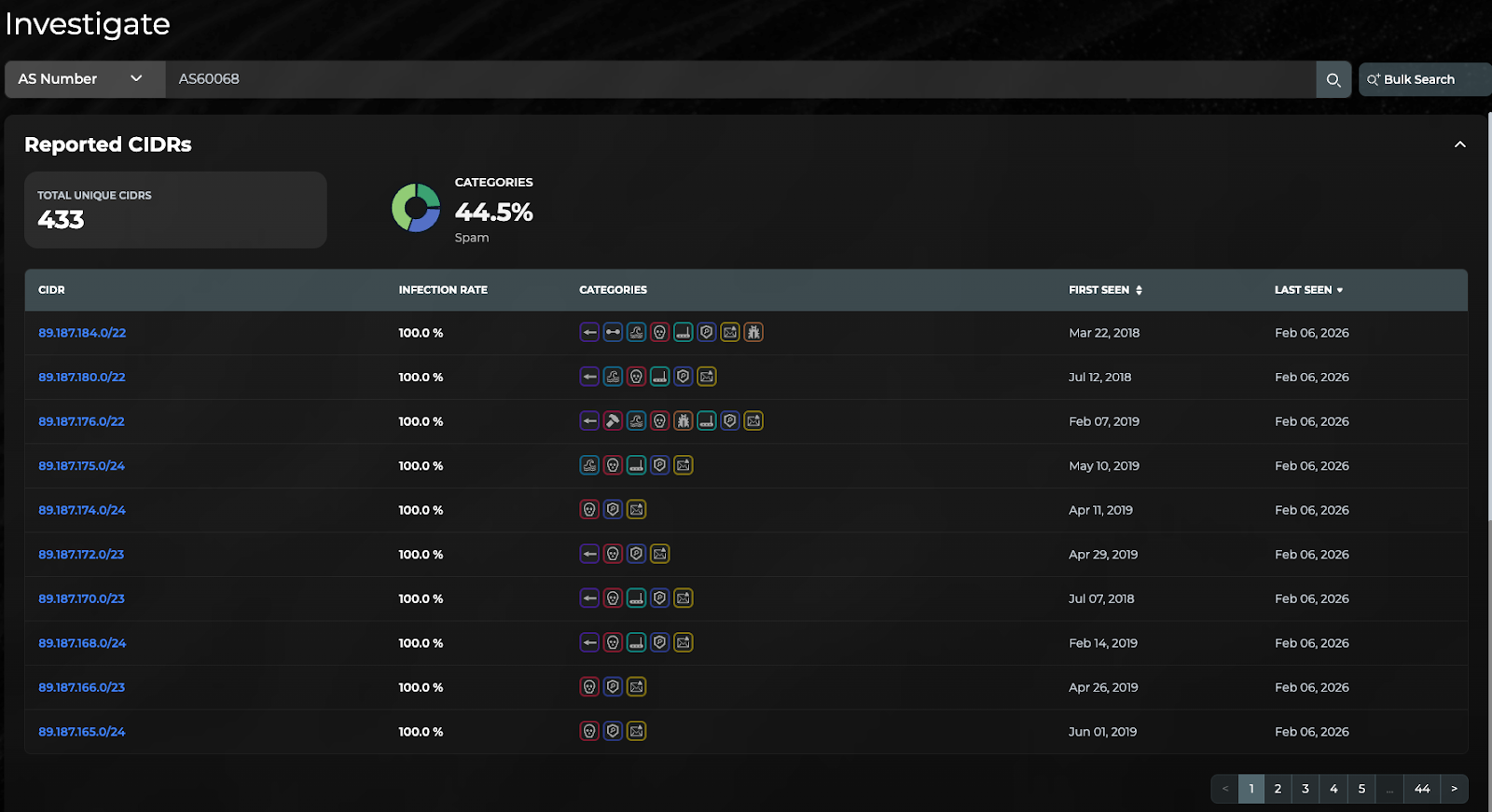
3.2 Sample from CDN77 - AS60068
Augur had advanced knowledge and identified significant elements of CDN77's infrastructure that protected our customers. In Image 1 below, several CIDRs of CDN77 have 100% infection rate, which means that all IPs within those CIDRs have been at least reported once with malicious activity, which is not uncommon for large networks but demonstrates that CDNs are also abused and involved in malicious activity.
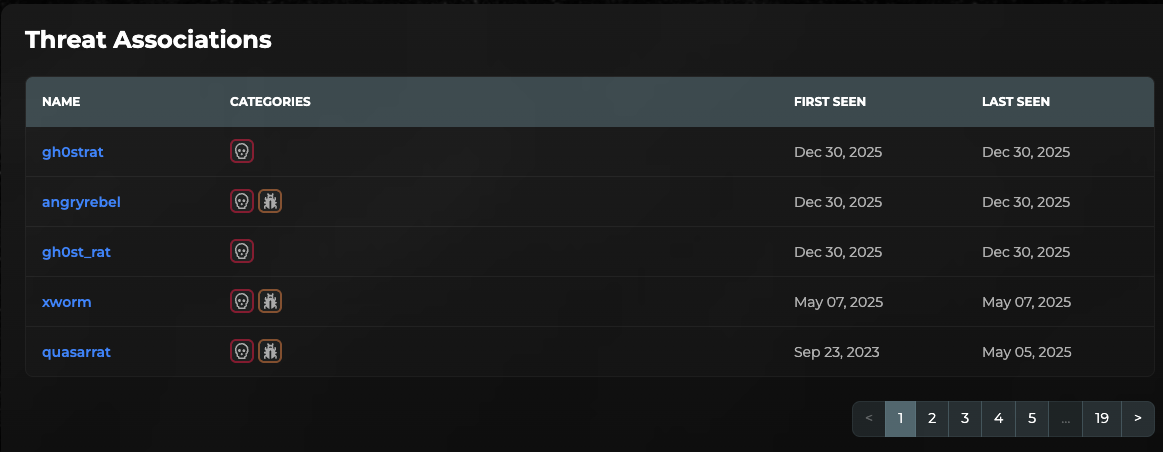
In Image 2 below, are some of the threats that have been observed across the CDN77 network, which includes several RATs, Infostealers, and other commodity malware.
3.3 Emerging Techniques
HTML Smuggling via SVG Files
Attackers embed malicious JavaScript in SVG image files via script tags; QBot campaigns use base64-encoded SVGs containing script code to smuggle malware onto victim systems.
Non-Script File Payload Embedding
Adversaries hide payloads from signature-based scanners by embedding code in images, icons, CSS, or JSON files. Examples include the Inter skimmer, which sends JSON under image URLs that appear as benign image fetches to scanners.
Multi-Stage Split Payload Delivery
Threat actors segment malicious functionality across multiple CDN-hosted resources, assembling complete payloads only at runtime in the victim's browser to evade static analysis.
4. Deep Dive: Tactical Analysis of CDN Exploitation
4.1 Abuse of Free Tier Services
Economic Model: Free CDN tiers eliminate financial barriers for threat actors. Cloudflare's free plan provides unlimited bandwidth; GitHub Pages offers free static hosting with global CDN distribution; and npm packages automatically receive CDN delivery via unpkg.com and jsDelivr. This creates a zero-cost attack infrastructure with enterprise-grade availability.
Operational Security Benefits: Free tiers typically require minimal identity verification and often accept disposable email addresses. Payment trails are eliminated, complicating financial attribution. Account creation can be automated, enabling rapid infrastructure rotation when accounts are suspended or terminated.
4.2 Trust Exploitation and Security Control Bypass
Domain Reputation Abuse: Security solutions commonly allow major CDN providers to prevent business disruption. Domains such as cloudflare.net, fastly.net, akamai.net, and cloudfront.net typically receive less scrutiny. Threat actors exploit this trust, knowing their malicious content benefits from the CDN's established reputation.
TLS Encryption as Evasion: Content from CDNs is delivered over TLS, hiding payloads from network-based scanners. Attackers can host malicious scripts or pages behind HTTPS to thwart inline inspection without HTTPS decryption.
URL Filtering Evasion: Traditional URL blocklists fail when malicious content resides on legitimate CDN domains. A malicious payload at cdn.jsdelivr.net/npm/malicious-package/payload.js appears identical in logs to legitimate library loads.
4.3 Attribution and Takedown Complexity
Shared Infrastructure Challenges: Multiple customers share CDN IP addresses and domains. Blocking a single IP address or domain can affect numerous legitimate users. Forensic investigations struggle to isolate specific customer traffic from aggregate CDN logs.
Jurisdictional Issues: CDNs operate globally with edge nodes in dozens of countries. Takedown requests are subject to varying legal frameworks and response times. Content cached at edge nodes may persist after the origin is removed, as demonstrated by the jsDelivr cache persistence issue.
Provider Responsiveness: Cloudflare's approach to abuse reflects the nature of infrastructure services, noting that it cannot remove content from the internet that it does not host. The vast majority of abuse reports concern pass-through security and CDN services rather than hosted content. This creates friction in abuse mitigation. CDN providers often forward complaints to hosting providers rather than taking direct action.
4.4 Detection Challenges
Legitimate vs. Malicious Traffic Differentiation: Detection challenges include the absence of reliable indicators of badness, as malicious content is served from legitimate CDN domains; network logs simply show access to domains like jsdelivr.net or cloudfront.net without payloads appearing malicious.
Unusual File Types and MIME Mismatches: Payloads may be hidden in unexpected file formats, such as .ico, .png, or .svg files that actually contain executable scripts or JSON exfiltration code, slipping past many scanners that expect image content.
Scriptless Attacks: Some CDN-hosted attacks use minimal or no active scripts, such as Webflow PDF phishing, which relies on fake CAPTCHA images embedded in PDFs with no obvious code to flag during static analysis.
4.5 Persistence and Resilience Mechanisms
Edge Cache Exploitation: Attackers leverage CDN caching behavior for persistence. Once malicious content enters edge caches, it propagates globally and may persist for extended periods even after origin takedowns.
Rapid Infrastructure Rotation: Free-tier abuse enables rapid account creation. When one account is suspended, attackers deploy identical infrastructure under new accounts within minutes. The Beamglea campaign demonstrated this with 175 packages across 9 accounts.
Distributed C2 Architecture: CDNs provide natural load balancing and failover for C2 infrastructure. Malware can connect to CDN endpoints that proxy traffic to backend C2 servers, with the CDN masking the actual C2 location.
5. Defensive Strategies and Recommendations
5.1 Network-Level Controls
Selective URL Filtering (Recommended Approach)
Instead of blocking CDN IP ranges, implement URL-based filtering focusing on specific paths and patterns:
- Monitor for newly registered packages on package CDNs (jsDelivr, unpkg.com)
- Block specific malicious resource paths while permitting known-good CDN traffic
- Implement allow-listing for critical CDN resources used by business applications
DNS-Based Protections
- Deploy DNS security solutions that analyze CDN subdomain patterns
- Block access to ephemeral CDN services (e.g., .trycloudflare.com) unless business-required
- Monitor DNS queries for unusual CDN subdomain patterns (long random strings, suspicious prefixes)
Enhanced Proxy and Firewall Configuration
- Configure SSL/TLS inspection for CDN traffic when operationally feasible
- Implement application-aware firewalls that can inspect CDN traffic beyond layer 3/4
- Create firewall rules restricting CDN access to approved applications and processes
5.2 Endpoint Detection and Response (EDR)
Behavioral Analysis
- Monitor for HTML files in Downloads folders containing CDN script references (especially unpkg.com, jsDelivr)
- Alert on processes fetching executables or scripts from CDN domains
- Detect unusual user-agent strings or connection patterns to CDN services
- Flag sequential navigation from local HTML files to external domains via CDN redirects
Process Monitoring
- Track suspicious child process creation following CDN resource loads
- Monitor for Python/PowerShell interpreters launched after CDN downloads
- Detect in-memory code execution following CDN-delivered payload retrieval
File System Monitoring
- Quarantine HTML attachments with embedded CDN references for analysis
- Monitor for files with MIME type mismatches (images containing scripts)
- Alert on creation of files in temporary directories following CDN downloads
5.3 Email Security Controls
Attachment Analysis
- Implement sandboxing for HTML email attachments
- Block or quarantine attachments with embedded CDN script references
- Analyze ZIP archives for suspicious LNK or BAT files referencing CDN URLs
URL Inspection
- Rewrite CDN URLs in emails to proxy through security gateways
- Implement time-of-click analysis for CDN URLs
- Detonate URLs in sandboxes to identify redirects to phishing pages
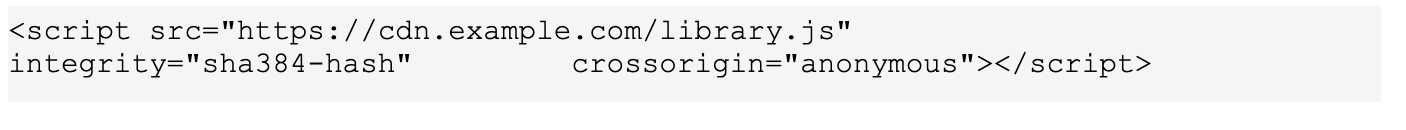
5.4 Web Application Security
Content Security Policy (CSP)
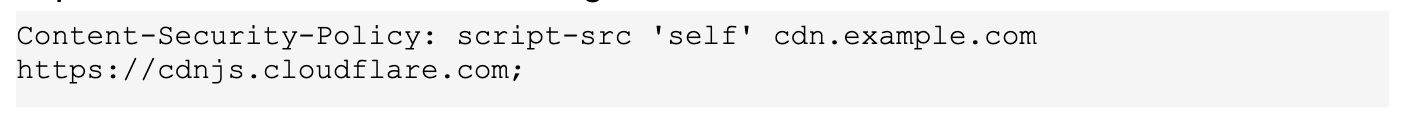
Subresource Integrity (SRI)
Dependency Monitoring
- Implement software composition analysis (SCA) tools
- Monitor package.json and dependency files for suspicious CDN-based packages
- Alert on newly published npm packages with low download counts
5.5 Threat Intelligence Integration
Indicator Enrichment
- Subscribe to threat intelligence feeds specific to CDN abuse
- Correlate internal CDN access logs with known malicious CDN paths
- Share indicators of compromise (IOCs) with industry peers through ISACs
Proactive Hunting
- Query EDR telemetry for historical access to known malicious CDN resources
- Analyze browser history for patterns matching CDN abuse campaigns
- Review firewall logs for unusual volume or timing of CDN requests
Package Repository Monitoring
- Monitor public package registries (npm, PyPI) for malicious packages
- Track takedown activities and cross-reference against internal logs
- Implement automated scanning of package metadata and code
Preemptive Cybersecurity
- Adopt preemptive cybersecurity techniques and technologies (like Augur) to identify and block threats before attacks launch and mitigate risk.
5.6 User Awareness and Training
Security Awareness Programs
- Train users to recognize phishing emails with HTML attachments
- Educate on risks of executing email attachments, especially .lnk, .bat, and HTML files
- Conduct phishing simulations using CDN-based delivery mechanisms
Developer Education
- Train development teams on supply chain security risks
- Implement code review processes for external dependencies
- Establish secure development practices, including dependency pinning
5.7 Incident Response Procedures
CDN Abuse Response Playbook
- Identification: Detect CDN abuse through EDR alerts, user reports, or threat intelligence
- Containment: Block specific malicious URLs/paths without disrupting legitimate CDN traffic
- Analysis: Determine scope, identify affected systems, compromised credentials, or data exfiltration
- Remediation: Remove malware, rotate credentials, restore from clean backups
- Reporting: Submit abuse reports to CDN providers with detailed evidence
- Recovery: Restore normal operations and validate no persistent access remains
Provider Engagement
- Establish relationships with CDN abuse teams for faster response
- Prepare standardized abuse report templates with technical evidence
- Participate in CDN provider bug bounty programs to improve security
6. Should Organizations Block CDN IP Addresses?
6.1 Arguments Against Blanket CDN IP Blocking
Critical Business Impact
Modern web applications depend extensively on CDNs. Blocking Cloudflare, Akamai, or Fastly IP ranges would immediately break:
- SaaS applications (Salesforce, Workday, ServiceNow)
- Cloud services (AWS CloudFront, Azure CDN, Google Cloud CDN)
- Internal applications using CDN-backed libraries (React, jQuery, Bootstrap)
- Communication platforms (Slack, Microsoft Teams)
- Security tools themselves (SIEM vendors, threat intelligence platforms)
Operational Ineffectiveness
CDN providers operate thousands of IP addresses across global PoPs. Maintaining accurate block lists is operationally infeasible:
- IP ranges change frequently as providers expand infrastructure
- Shared IP addressing means blocking affects thousands of legitimate sites
- Cloud-based CDNs use dynamic IP allocation, making static blocking ineffective
Circumvention and Adaptation
Threat actors would simply adapt by:
- Using different CDN providers (hundreds exist)
- Leveraging non-CDN infrastructure
- Exploiting alternative legitimate services (cloud storage, collaboration platforms)
Limited Security Value
Network operators cannot indiscriminately block CDN infrastructure when malicious abuse is detected, as they must differentiate between legitimate and malicious traffic, which is challenging when threat actors employ sophisticated techniques to blend in with legitimate CDN traffic.
6.2 Risk-Based Assessment Framework
Organizations should assess CDN blocking based on:
Business Dependency Analysis
- Document all business-critical applications using CDNs
- Identify which CDN providers support essential services
- Calculate potential downtime costs from CDN blocking
Threat Landscape Evaluation
- Assess the organization's exposure to CDN-based threats based on industry
- Review historical incidents involving CDN abuse targeting the organization
- Evaluate existing security controls' effectiveness against CDN threats
Risk Tolerance
- High-security environments (financial services, defense) may accept limited functionality loss for enhanced security
- Organizations with lower risk appetites should prioritize detection over blocking
6.3 Selective Blocking with Enhanced Monitoring
Tiered CDN Trust Model:
Tier 1 - Full Trust (No Blocking)
- Enterprise CDNs supporting critical SaaS applications
- Internal applications' documented CDN dependencies
- Vendor-specific CDNs for approved business applications
Tier 2 - Enhanced Monitoring (No Blocking, Active Detection)
- Major public CDNs (Cloudflare, Akamai, Fastly, Bunny CDN)
- Package CDNs (jsDelivr, unpkg.com, cdnjs)
- Implement deep packet inspection where feasible
- Deploy behavioral analytics on endpoints
Tier 3 - Conditional Blocking
- Free/ephemeral CDN services (trycloudflare.com, temporary subdomains)
- Less common CDNs without documented business use
- Recently established CDN providers with limited reputation
- Block by default, allow specific resources as needed
Tier 4 - Default Block
- CDN services predominantly associated with abuse
- Providers with poor abuse response track records
- Services offering highly anonymous temporary hosting
6.4 Alternative Mitigation Strategies
Instead of IP-based blocking, organizations should:
- Implement Zero Trust Architecture: Verify every request, regardless of source, including CDN traffic
- Deploy Advanced Threat Protection: Use EDR, NDR, and SIEM to detect anomalous CDN usage patterns
- Enforce Application Allowlisting: Restrict which applications can access CDN resources
- Utilize Cloud Access Security Brokers (CASB): Inspect and control cloud/CDN traffic
- Adopt Secure Web Gateways (SWG): Filter web traffic at URL/content level rather than IP level
6.5 Final Assessment
Organizations should understand the risks of broad CDN IP blocking: it can cause significant business disruption, offers limited security gains against adaptive attackers, and more effective, less intrusive security controls are available in a rapidly changing threat environment. Instead, they should implement layered, behavior-focused defenses, use endpoint and network analytics to spot CDN abuse, apply targeted blocking only to high-risk CDN services with limited business impact, invest in threat intelligence and proactive hunting, and build fast abuse-reporting channels with CDN providers. In tightly controlled environments such as air-gapped or classified systems, selectively blocking certain CDN categories may be appropriate, but only when supported by a thorough business impact analysis, alternative content delivery options, clearly documented security policies, and regular review of blocked content.
7. Conclusion
Content Delivery Networks represent dual-use infrastructure essential for modern internet functionality, yet attractive to threat actors seeking to abuse trusted platforms. The CDN threat landscape since January 2025 has demonstrated increasingly sophisticated exploitation techniques, ranging from NPM package abuse for phishing infrastructure to Cloudflare Tunnel manipulation for malware delivery.
Organizations must adopt nuanced security approaches that incorporate preemptive cybersecurity measures (like Augur) to balance risk mitigation with operational requirements. Blanket CDN IP blocking could create more problems than it solves, disrupting business operations while providing minimal security benefit against adaptive adversaries. Instead, security teams should implement detection-focused strategies leveraging behavioral analytics, threat intelligence integration, and selective access controls.
The ongoing evolution of CDN abuse tactics requires continuous monitoring, threat hunting, and adaptation of defensive measures. Success depends not on complete CDN blocking but on intelligent differentiation between legitimate and malicious CDN usage through modern security architecture.
Take a deeper dive into Preemptive Cybersecurity:
What is Preemptive Cybersecurity and why does it matter?
How does Preemptive Cybersecurity prevent AI-powered and Agentic AI attacks?
AI changed the game in 2025, and Augur was there to protect against zero-days and novel threats
8. Sources and References
- 175 Malicious npm Packages with 26,000 Downloads Used in Credential Phishing Campaign: https://thehackernews.com/2025/10/175-malicious-npm-packages-with-26000.html
- 175 npm packages, unpkg CDN abused for phishing infrastructure: https://www.scworld.com/news/175-npm-packages-unpkg-cdn-abused-for-phishing-infrastructure
- FatalRAT Phishing Attacks Target APAC Industries Using Chinese Cloud Services: https://thehackernews.com/2025/02/fatalrat-phishing-attacks-target-apac.html
- Analyzing SERPENTINE#CLOUD: Threat Actors Abuse Cloudflare Tunnels to Infect Systems with Stealthy Python-Based Malware: https://www.securonix.com/blog/analyzing_serpentinecloud-threat-actors-abuse-cloudflare-tunnels-threat-research/
- New Malware Campaign Uses Cloudflare Tunnels to Deliver RATs via Phishing Chains: https://thehackernews.com/2025/06/new-malware-campaign-uses-cloudflare.html
- Cloudflare Tunnels Abused in New Malware Campaign: https://www.securityweek.com/cloudflare-tunnels-abused-in-new-malware-campaign/
- Cloudflare's developer domains increasingly abused by threat actors: https://www.bleepingcomputer.com/news/security/cloudflares-developer-domains-increasingly-abused-by-threat-actors/
- 13,000+ Malicious Domains Emerge as Hackers Exploit Cloudflare in Clickfix Campaign: https://cyberpress.org/clickfix-campaign-cloudflare/
- Massive NPM Supply-Chain Attack Infects Developers During Package Installs: https://cyberpress.org/npm-supply-chain-attack-2/
- Abusing Content Delivery Networks (CDNs): Phishing, Malware, and Evasion: https://blogs.night-wolf.io/abusing-content-delivery-networks-cdns-phishing-malware-and-evasion
- Abused CDNs: From Speedy Content to Stealthy Malware: https://blogs.juniper.net/en-us/threat-research/abused-cdns-from-speedy-content-to-stealthy-malware
- CDN Service Exposes Users to Malicious Packages for Phishing Attacks Invisible to Security Tools: https://blog.checkpoint.com/securing-the-cloud/cdn-service-exposes-users-to-malicious-packages-for-phishing-attacks-invisible-to-security-tools/
- New Attack Abuses CDNs to Spread Malware: https://www.securityweek.com/new-attack-abuses-cdns-spread-malware/
- 5 Key Security Risks Associated with CDN Operations: https://www.ioriver.io/blog/security-risks-for-cdn-operations
- Google User Content CDN Used for Malware Hosting: https://www.bleepingcomputer.com/news/security/google-user-content-cdn-used-for-malware-hosting/
- Critical Cloudflare CDN flaw allowed compromise of 12% of all sites: https://www.bleepingcomputer.com/news/security/critical-cloudflare-cdn-flaw-allowed-compromise-of-12-percent-of-all-sites/
- Cloudflare CDN spills location data with simple hack: https://www.theregister.com/2025/01/27/cloudflare_cdn_location_data/
- Abuse approach - Cloudflare: https://www.cloudflare.com/trust-hub/abuse-approach/
- Report abuse to Cloudflare: https://developers.cloudflare.com/fundamentals/reference/report-abuse/