1. Executive Summary
Augur Security has identified Storm-1175 aggressively weaponizing critical vulnerabilities in internet-facing assets to facilitate high-velocity ransomware campaigns. Operators have been observed advancing from initial compromise to full data encryption within 24 hours, severely limiting defensive response windows. Augur is issuing this threat flash to highlight preemptively identified infrastructure currently active during Storm-1175’s campaign. Proactive mitigation of this infrastructure is essential to blocking Storm-1175 at the perimeter and avoiding a campaign that consistently outpaces defender reaction time.
1.1 Background
Storm-1175 operates as a financially motivated ransomware actor within the wider Medusa ecosystem. The group specializes in blitz operations targeting newly exposed vulnerabilities in administrative interfaces and perimeter security layers, often targeting those that are public-facing. Between 2025 and 2026, the group’s increased operational speed and technical skill elevated it as one of the more persistent ongoing threats to internet-facing infrastructure. Operators aggressively exploit enterprise web applications through newly disclosed vulnerabilities and Zero Days, moving quickly from access to exfiltration. Augur has documented this targeting across healthcare, education, and finance, with some cases culminating in full environmental encryption within 24 hours.
Public reporting in 2025 also linked Storm-1175 to the exploitation of the GoAnywhere Managed File Transfer deserialization flaw (CVE 2025-10035). This campaign was consistent with the actor’s tradecraft, displaying their traditional smash-and-grab method; a tactic that exploits the window between vulnerability disclosure and patching for easy infiltration. By compressing the timeline from initial disclosure to infiltration and extortion, Storm-1175 is able to deploy Medusa across dozens of industries and circumvent traditional dwell-time detection. Separate reporting later identified the group chaining multiple exploits for post-compromise activity and utilizing at least three zero days, including CVE-2026-23760 in SmarterMail. Operators frequently weaponize vulnerabilities roughly a week before public disclosure, significantly increasing the risk to unpatched systems. Augur tracking alone has linked the actor to the exploitation of more than 16 vulnerabilities since 2023, confirming a pattern of rapid weaponization that consistently limits the effectiveness of traditional perimeter defense.
2. Exploitation
Storm-1175 demonstrated extreme operational velocity in late September 2025 by weaponizing a zero-day deserialization flaw in Fortra’s GoAnywhere MFT (CVE-2025-10035). Operators exploited the License Servlet to achieve pre-authentication remote code execution (RCE) via the Admin Console, transitioning to hands-on keyboard activity eight days before the vulnerability was publicly disclosed. To maintain control, operators deployed SimpleHelp and MeshAgent binaries directly under the GoAnywhere process. Persistence was solidified by injecting malicious JSP files into internal directories, while lateral movement relied on a native mstsc.exe (RDP) binary after network mapping via netscan. Command-and-control (C2) traffic was masked via Cloudflare tunnels, while data exfiltration was conducted using Rclone, an open-source file transferring tool. After extensive file exfiltration, operators ended with the deployment of Medusa ransomware.
The use of Cloudflare tunnels highlights a broader industry trend: attackers increasingly rely on trusted edge infrastructure to blend malicious traffic with legitimate activity, making traditional detection-based approaches insufficient.
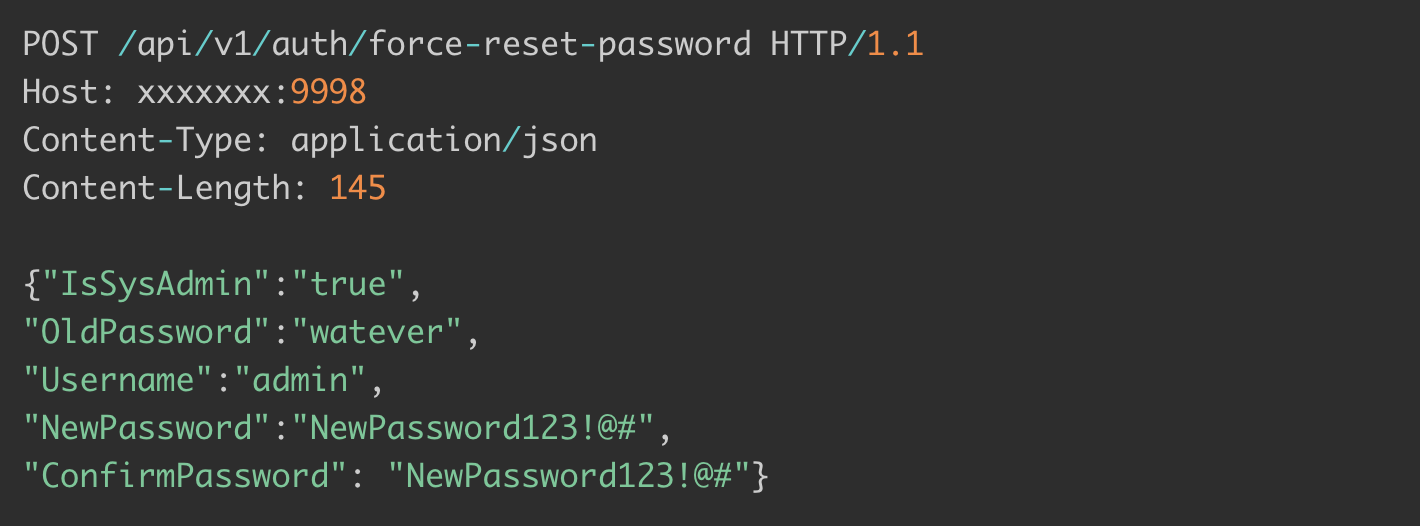
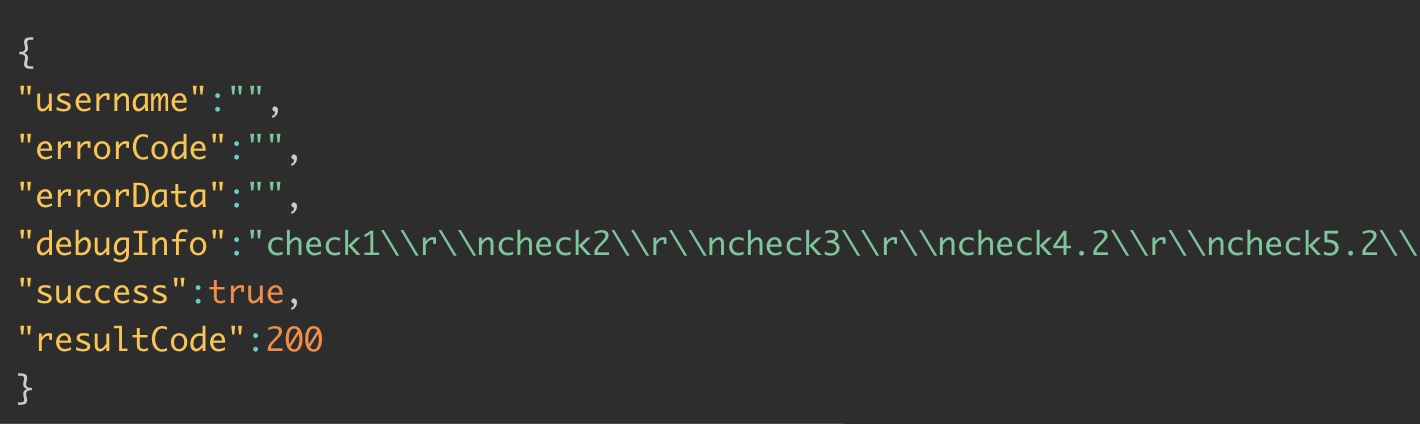
The current March to April 2026 offensive reflects a broader, more destructive exploitation model. Storm-1175 is currently weaponizing CVE-2026-23760 in SmarterMail through a critical flaw in the force-reset-password API. This vulnerability allows unauthenticated actors to hijack the reset flow and create fraudulent system administrator accounts, allowing full mail server compromise. Upon takeover, the actor abuses unauthorized administrator accounts to exfiltrate data and modifies host firewall rules to enable persistent RDP access.
Recent tracking links this campaign to high-impact disruptions across a variety of targets, the city government of Passaic County, New Jersey and the University of Mississippi Medical Center to name a few. The assault on the medical center forced a transition to manual operations after its Epic electronic health record system went offline, showing the severe operational degradation Storm-1175 can achieve once initial access is secured. Augur assesses that these campaigns are engineered to inflict maximum extortion pressure, often outpacing containment efforts to create a visible impact on public-facing applications. Current tracking identifies this same campaign actively targeting multiple sectors, indicating an expanding threat.

3. Actor Overview
Storm-1175 operates as a China-based, financially motivated intrusion actor associated with the wider Medusa ransomware ecosystem. Augur assesses the cluster's primary motivation to be financial, with activity indicative of a ransomware affiliate rather than a state-directed actor (though infrastructure overlap with PRC-linked tooling warrants continued monitoring). The defining characteristic of the cluster is extreme operational speed, with the demonstrated ability to weaponize vulnerabilities as Zero Days or N-Days. Recent intelligence confirms Storm-1175 leverages a sophisticated exploitation pipeline to chain N-day and zero-day flaws, allowing them to deploy ransomware in as little as twenty four hours. Augur also places the cluster’s activity across the United States, the United Kingdom, and Australia, and ties the actor to exploitation of more than 10 product families since 2023, indicating a broad access-focused operator.
The technical tradecraft of Storm-1175 focuses on blending malicious activity with legitimate administrative traffic. The group relies on a rotating suite of legitimate remote monitoring and management tools, like SimpleHelp, MeshAgent, and Atera, to maintain persistence and facilitate lateral movement. For command and control, operators frequently mask traffic within Cloudflare tunnels and utilize Rclone for data exfiltration. Persistence is often solidified by creating unauthorized administrator accounts and disabling security software through registry and firewall modifications, ensuring the environment is primed for the final deployment of Medusa ransomware.
Storm-1175 targeting remains opportunistic, with a focus on high-impact sectors, including but not limited to healthcare, education, finance, and professional services. High-profile disruptions linked to the wider Medusa network have targeted Minneapolis Public Schools and Toyota Financial Services, and have also breached county government systems in the U.S. and the UK. Storm-1175’s strategy focuses on organizations where operational downtime increasingly strains the victim, thereby guaranteeing operators maximum extortion leverage. Current telemetry indicates that Storm-1175 continues to aggressively scan for exposed perimeter assets across these sectors.
4. Augur Assessment
Augur predictive intelligence identified and blocked the core operational infrastructure for Storm-1175 years before public attribution. The earliest confirmed prediction dates to June 22, 2017, when Augur flagged 213.183.32.0/19—the Melbicom netblock containing 213.183.63.41 -- as malicious infrastructure. This designation (Importance: 80/100, Category: Malware) followed behavioral activity observed as early as April 2017. Subsequent cluster predictions occurred in November 2019 (45.11.183.0/24, Profile 112167, Importance: 80/100), August 2022 (45.133.1.0/24, Profile 155115, Importance: 60/100), and December 2020 (185.135.86.0/24, Profile 139722, Importance: 60/100). Microsoft did not publicly designate the group or attribute this infrastructure until October 6, 2025, with the full indicator set remaining undisclosed until April 6, 2026. Augur’s lead time across these indicators ranges from 170 days to nearly 9 years, representing detection and blocking at the network perimeter before the broader threat intelligence community had visibility into the actor or its campaign.
The phishing domain departmentofdefence[.]live (infrastructure publicly attributed to campaigns targeting the Modi government in India) was ingested into the Augur database on October 17, 2025. This occurred a week prior to the first actor attributed public report and nearly six months before the domain was linked to the Storm-1175 context. Augur began tracking the broader departmentofdefence[.]* phishing infrastructure across multiple top-level domains (.cc, .link, .pl, .online, .nl, .ml, .com, .de) as early as January 24, 2025. This effort cataloged 53 host-type indicators spanning the full campaign footprint, a scope that exceeded any single public report at the time. Augur’s cluster-based behavioral predictions consistently identified Storm-1175 infrastructure through patterns of malicious hosting, providing confirmed pre-detection and blocking coverage across all verified indicators associated with the current exploitation campaign.

5. Co-Location
Beyond pre-detection lead time, the behavioral clusters constructed by Augur around this infrastructure independently corroborate the China-based attribution of Storm-1175. Profile-139722, the cluster anchoring the 185.135.86.0/24 insight, recorded confirmed co-detections of Naikon, Stately Taurus, CeranaKeeper, RedDelta, MQSTTang, ToneShell, and PocoDown. These are all PRC-linked APT tooling families that remained active within that specific cluster throughout March 2026. Profile-112167, which anchored the 45.11.183.0/24 prediction, was also co-located to APT31 alongside FIN 7, Cobalt Strike, and LockBit. Notably, APT 31 is a confirmed Chinese state actor, further supporting Augur’s existing geographic and operational tracking of the operators.
The earliest cluster, Profile-58415 on the 213.183.32.0/19 Melbicom block, detected Crimson RAT and PowerStats as early as 2016. These tools are independently attributed to APT 36 (Transparent Tribe), the same actor that publicly claimed the departmentofdefence[.]live infrastructure in October 2025. The overlap between APT 36 tooling in the 2017 Melbicom cluster and the actor’s subsequent use of the phishing domain within the same campaign suggests a durable infrastructure relationship on shared Melbicom hosting that predates public visibility by nearly a decade. Augur’s cluster model provided visibility into the surrounding actor ecosystem as well, providing early behavioural signals for both the infrastructure and threat communities operating within it.
Augur’s cluster model captured an ecosystem where diverse threat actors—ranging from Chinese state-aligned groups to regional espionage clusters like APT 36—occupy overlapping network space. That overlap places Storm-1175 in network space consistently associated with mature, higher capability operators; a warning signal for defenders and analysts alike.
Figure 5: Preemptively Identified IOCs associated with Storm-1175 campaign
6. Mitigation
The operational velocity of Storm 1175 necessitates a shift to proactive attack-surface reduction and malicious-infrastructure blocking. Defending against an adversary that weaponizes vulnerabilities within hours of disclosure requires robust hardening to ensure that malicious attacks never make it past the perimeter. Organizations should isolate internet-facing assets behind secure network boundaries and enforce rigorous application control policies. This allows enterprise organizations to disrupt the initial access and lateral movement tradecraft that Storm-1175 relies on for rapid environmental infiltration and encryption. Effective defense hinges on eliminating the "dwell time" opportunities that these actors exploit to transition from a single compromised edge device to a full-scale ransomware deployment.
- Preemptive Infrastructure Monitoring and Blocking: Incorporate infrastructure-level monitoring to identify and restrict communication with Augur-identified malicious CIDRs and hosting environments prior to exploitation. Leveraging behavioral clustering and threat intelligence to enforce egress controls disrupts adversary infrastructure before it is operationalized in campaigns. Aggressive blocking limits an actor’s ability to establish command-and-control, stage payloads, or maintain persistence within the environment.
- Harden Edge Infrastructure and Perimeter Assets: Organizations must prioritize the immediate patching of critical vulnerabilities in MFT solutions and administrative gateways, such as GoAnywhere and SmarterMail. To mitigate zero-day risk, all internet-facing management interfaces should be restricted to VPN or zero-trust access and placed behind a Web Application Firewall (WAF) to filter malicious exploitation attempts.
- Restrict and Monitor Administrative Tooling: Defenders should implement strict application allowlisting to block unauthorized remote monitoring and management (RMM) tools like SimpleHelp, MeshAgent, and Atera. C-level stakeholders must ensure that even sanctioned administrative tools require multi-factor authentication and are continuously monitored for LOL (living-off-the-land) behaviors that deviate from baseline IT operations.
- Disrupt Exfiltration and Lateral Movement Channels: Security teams must monitor for and block the unauthorized use of Cloudflare tunnels and data synchronization utilities like Rclone. Implement network segmentation and disable Remote Desktop Protocol (RDP) on all non-essential internal systems to significantly hinder an operator’s ability to pivot from initial breach to data exfiltration.
7. Conclusion
Storm-1175 represents an active, high-tempo threat where Augur’s predictive threat intelligence enables pre-emptive blocking, providing a crucial defensive advantage. The actor's ability to operationalize zero-day vulnerabilities before public awareness, alongside a proven disruption strategy designed to maximize extortion pressure, warrants immediate and sustained defensive posture.
Augur continues to monitor Storm-1175 infrastructure, affiliate activity, and emerging exploitation patterns to provide advance warning ahead of the broader threat intelligence community.
The level of lead time provided by Augur enables a fundamentally different defensive model when paired with modern edge platforms. By integrating Augur’s infrastructure intelligence into enforcement points such as Cloudflare’s global network, organizations can automatically block adversary-controlled IP space and domains before they are used in active campaigns, eliminating the attacker’s ability to establish initial access or command-and-control channels.
Contact: research@augursecurity.com
8. Sources
- Actively Exploited GoAnywhere MFT Zero- Day Vulnerability (CVE-2025-10035) | eSentire
- Fortra GoAnywhere MFT Attack | Outbreak Alert | FortiGuard Labs
- Investigating active exploitation of CVE-2025-10035 GoAnywhere Managed File Transfer vulnerability | Microsoft Security Blog
- Why Perimeter Firewall is Not Enough: Lessons from the GoAnywhere MFT Zero-Day - VMware Security Blog
- CVE-2025-10035 Exploit: Storm-1175 Attack on GoAnywhere MFT | Hive Pro
- Microsoft links Medusa ransomware affiliate to zero-day attacks




