1) Context
NoName057 hit the headlines again at the start of the 2026 Winter Olympics in Milan-Cortina, launching a series of DDoS attacks using its proprietary DDoSia attack toolkit. (read about it here)
At Augur Security, we’ve been tracking the pro-Russia hacktivist collective "NoName057(16)," which has targeted European and American critical infrastructure and government services since its emergence during the 2017-era wave of Russian information operations. And we identified more than 35 CIDRs (containing more than 8k IP addresses) associated with NoName057 activities on average, more than 60 days before they were operationalized (meaning if you were a target, you had significant protection with Augur).
1.1) Background: Not Their First Rodeo
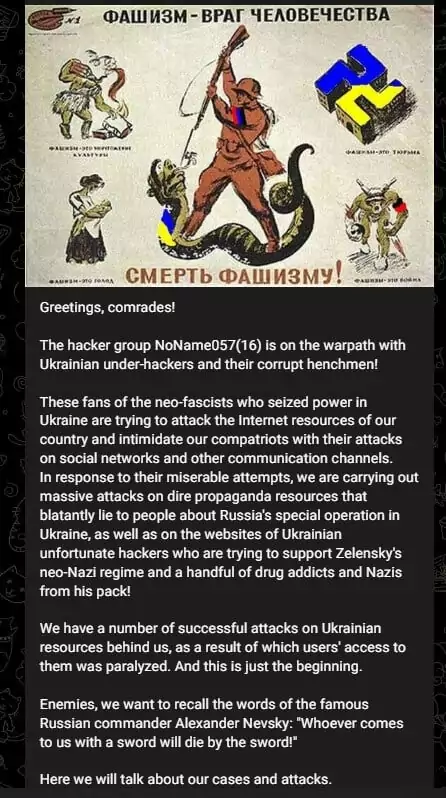
While initially a decentralized entity, the group has evolved into a significant disruptive force specializing in high-volume Distributed Denial-of-Service (DDoS) campaigns designed to paralyze state websites and client-facing applications. Despite multiple international law enforcement efforts, including the 2025 "Operation Eastwood" which dismantled significant portions of their server infrastructure, NoName057(16) remains a persistent and adaptive threat. The group continues to serve as a primary tool in Russian information warfare, using its proprietary DDoSia project to mobilize and reward a volunteer "cyber army" to exert geopolitical pressure on NATO-aligned nations.
1.2) Current Target: Olympics
The group’s current tactical focus is the February 2026 campaign targeting the Milan-Cortina Winter Olympics. This live operation has already seen NoName057 claim responsibility for strikes against the Italian Ministry of Foreign Affairs (MAECI), hospitality infrastructure in Cortina d'Ampezzo, and several foreign Olympic Committee websites. These attacks demonstrate a shift toward "event-driven" targeting, where the group exploits the high media visibility of
international competitions to amplify its narrative of retaliation for Western support of Ukraine. Augur Security assesses that these high-profile disruptions frequently serve as tactical intelligence-gathering for the allied Sandworm Team (APT44); the "noise" generated by
NoName057 covertly allows state-sponsored actors to identify defensive bottlenecks and test network resilience under stress. Campaigns like these allow NoName057 to function as a
strategic force multiplier, giving the Russian state a mechanism to degrade foreign infrastructure and dominate the digital narrative during high-stakes global events.
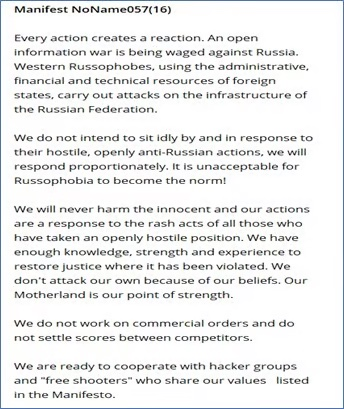
2) NoName057 Governance, Structure, and Operations
NoName057 operates a large-scale, participatory Denial-of-Service operation powered by its DDoSia Project. This affiliate program incentivizes independent operators to supply digital resources by offering cryptocurrency rewards (primarily in TON or Bitcoin) to those who demonstrate the highest volume of successful requests. The core of their offensive capability is the proprietary DDoSia tool, a Go-based multi-platform client (Windows, Linux, macOS, Android) that automates the targeting of victims. While the group claims a volunteer base of thousands, its core technical engine relies on several hundred high-performance servers to amplify the volume of these volunteer-led strikes.
The group maintains high operational synergy with other Russian-aligned entities, including KillNet, XakNet, and the Cyber Army of Russia Reborn (CARR). This collaboration (often referred to as the “Z-alliance”) frequently results in "joint strikes" and infrastructure sharing, particularly in campaigns targeting the energy and transportation sectors. Adhering to the Kremlin’s laissez-faire policy toward patriotic hacking, NoName057 strictly avoids targeting Russia or the Commonwealth of Independent States (CIS). Instead, their operations are reactive and event-driven, with attacks typically occurring within 24–48 hours of Western geopolitical shifts, such as announcements of new EU sanctions, NATO military aid packages, or, most recently, the exclusion of Russian athletes from the 2026 Winter Olympics.
While NoName057 presents as a grassroots movement formed in March 2022, its infrastructure is a state-sanctioned project. U.S. and European intelligence (specifically through Operation Eastwood in July 2025) have linked the group to the Center for the Study and Network Monitoring of the Youth Environment (CISM), an IT organization established by a 2018 Russian Presidential Decree. Far from its public mandate of "protecting Russian youth from harmful content," CISM provided the covert laboratory where state-employed engineers developed the DDoSia tool and continue to select targets. This state-backed foundation allowed the group to survive a massive 2025 law enforcement takedown, reconstituting its C2 infrastructure within days to begin its current offensive against the Milano Cortina Games.
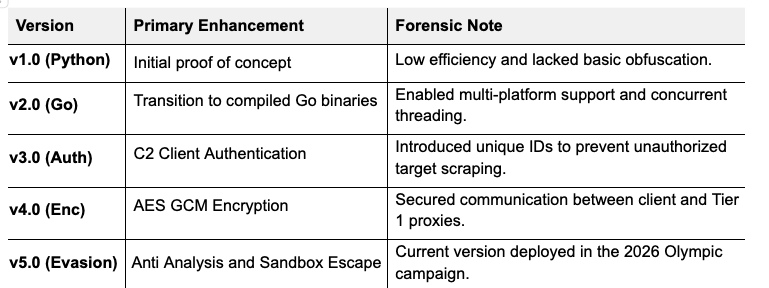
3) Methodology and Tooling
NoName057 relies on a proprietary toolkit named DDoSia, which has undergone rapid technical maturation since its inception. Augur Security has authenticated five distinct versions of the tool. Recent iterations have introduced encrypted Command and Control (C2) communication using AES-GCM encryption and automated proxy rotation to bypass traditional network filtering. To thwart forensic analysis and research efforts, the latest builds incorporate anti-debugging features, sandbox escape mechanisms, and the ability to rotate User Agent strings to mimic legitimate browser traffic. The group has successfully expanded the tool footprint beyond Windows, releasing native Go-based variants for Linux, macOS, and Android, as well as Dockerized versions. The group manages this arsenal through a resilient multi-tiered C2 infrastructure. The DDoSia client initiates communication with ephemeral Tier 1 proxies, which typically rotate every nine days, to shield the backend Tier 2 servers from detection. These core servers act as the operational brain of the collective, hosting the volunteer database and automating target distribution to the botnet. Access to the Tier 2 backend is strictly governed by Access Control Lists (ACLs) that only permit traffic from authorized Tier 1 nodes, ensuring the central infrastructure remains insulated even if individual proxies are seized or sinkholed by law enforcement.
Within this backend environment, NoName057 operates its affiliate program by transforming international sabotage into a gamified gig economy. By maintaining a public leaderboard, the group incentivizes volunteers to compete for rankings and financial payouts. Top performers receive rewards in dCoin, an internal digital currency that participants can convert into TON (The Open Network) cryptocurrency for withdrawal to private wallets. This decentralized payment structure allows the group to treat cyber warfare as a routine commercial service while masking the hand of the Russian state behind a global crowd of paid affiliates.
4) Known Victims
NoName057 has targeted platforms in over 40 countries to date, with the vast majority of operations focusing on Western nations and Ukraine. While the group continues to strike federal websites in the United Kingdom and United States, its primary mission is the systematic disruption of the NATO-aligned states supporting the Ukrainian defense. Through its primary Telegram channel, NoName057 has recruited over 45,000 subscribers and several thousand active volunteers to participate in the DDoSia Project. Augur Security has verified that this botnet has expanded significantly, leveraging a hybrid network of compromised servers and volunteer machines to launch multi-vector attacks against the strategic enemies of the Russian Federation.
The group's current tactical priority is the February 2026 campaign against the Milano Cortina Winter Olympics. This operation is a retaliatory strike against Italy for its pro-Ukraine foreign policy and serves as a high-visibility protest against the exclusion of Russian athletes. Augur Security believes NoName057 will sustain this aggressive campaign throughout the Games, leveraging the international media spotlight to amplify its message of Russian resilience and Western vulnerability.

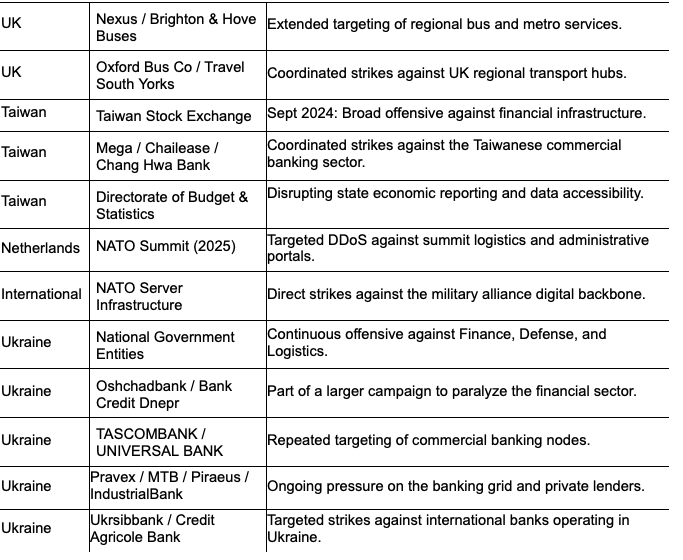
Beyond public disruption, this Olympic campaign serves a dual purpose as a strategic intelligence operation. By generating a high volume of network noise across 120 unique Italian domains, including hospitality infrastructure and diplomatic outposts in Washington and Paris, NoName057 effectively maps defensive response times and identifies bottleneck vulnerabilities. This activity provides the Russian state with live telemetry on Western infrastructure resilience while simultaneously providing cover for more clandestine actors (like Sandworm Team) to conduct probing undetected.
5) Technical Indicators
The following indicators of compromise (IOCs), identified by Augur, are linked to this activity. Augur advises CISOs, security teams, and SOC analysts to monitor for any interactions or communications with these indicators, as they may signal active targeting or compromise.


Augur has observed that several infrastructure profiles and hosting patterns associated with the indicators above overlap with infrastructure linked to advanced persistent threat (APT) activity and financially motivated intrusion sets. This overlap reflects a strategic reliance on specialized hosting providers and relay services that prioritize operational anonymity. Specifically, the group utilizes infrastructure that shares significant telemetry with Unit 74455 (Sandworm) and the hybrid collective Z-Pentest, indicating a shared resource pool authorized by the Russian state. While these groups maintain distinct tactical objectives, their use of common hosting providers ensures that NoName057 operations remain resilient against takedown efforts such as Operation Eastwood in mid-2025.
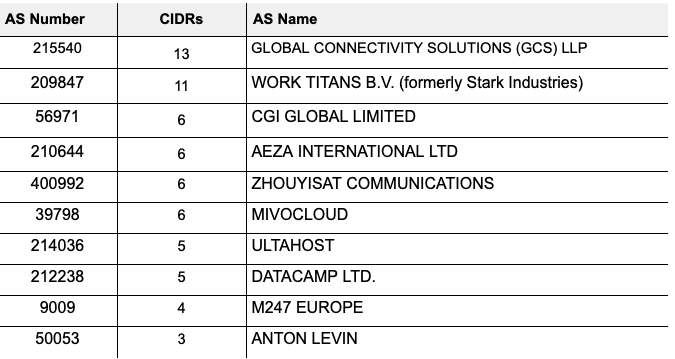
The threat actor appears to acquire IPs from specific providers we are familiar with, as shown in the analysis Top 10 table below (the full table is available in Appendix A). To note, we have had early knowledge of their CIDRs. Some of the bulletproof hosts below are well-known, such as WorkTitans, a rebrand of Stark Industries, and Mivocloud, which was used during the SolarWinds attack perpetrated by APT29.
6) Recommendations for CISOs
Augur Security’s analysis of NoName057 campaigns from 2022 through early 2026 confirms a high-fidelity correlation between digital disruption and real-life friction. For security operations, NoName057 is no longer just a "nuisance" actor but a geopolitical bellwether. Their activity spikes act as a leading indicator, often telegraphing major policy shifts or military announcements 24 to 72 hours before they are made public.
To defend against NoName057, their evolving "Z-Alliance", and the persistent DDoSia project, CISOs should prioritize the following three pillars:
6.1 Proactive Infrastructure Intelligence
Organizations must go beyond blocking known bad IPs. NoName057 uses a multi-tiered infrastructure in which Tier 1 C2 servers act as ephemeral proxies (often rotated daily). To that end, businesses must use proactive cybersecurity tools (such as Augur) to prevent attacks before they occur.
- Action: Shift to behavioral DDoS mitigation. Security teams must prioritize identifying HTTP/2 Rapid Reset sequences and spoofed TLS fingerprints, as the v5.0 DDoSia client now mimics legitimate Chrome and Firefox traffic to bypass signature-based WAF rules. Monitor for encrypted AES-GCM payloads directed at /client/login endpoints to flag internal compromised nodes before volumetric strikes begin.
6.2 Nuisance Resilience
A core objective of these hacktivists is "Cognitive Warfare". Eroding public trust by making legitimate government services appear fragile during high-stakes events (e.g., elections or summits).
- Action: CISOs should treat DDoS protection as a reputational safeguard. This involves ensuring that public-facing portals are hosted on redundant, geographically distributed cloud scrubbing centers (like AWS Shield or Cloudflare). These redundancies ensure "zero-downtime" optics during high-profile events like the 2026 Winter Olympics, even if the underlying infrastructure is under heavy load.
6.3 Geopolitical-Cyber Awareness
The lead-in times identified in this report (averaging 48 hours for summits and 24 hours for kinetic strikes) prove that cyber defense cannot exist in a vacuum.
- Action: Security teams must integrate Geopolitical Risk Indicators (GRI) into their SOC workflows. If a major "Red Line" shift is detected in diplomatic channels (like new weapon transfers or NATO accession talks), SOC alert thresholds should be lowered immediately. Given the Z-Alliance pivot toward infrastructure sabotage, SOC playbooks must now include the immediate isolation of internet-exposed HMI and VNC panels when geopolitical triggers are met.
As of 2026, NoName057 has survived major international takedowns, including Operation Eastwood, by leveraging the engineering and infrastructure backbone provided by the Center for the Study and Network Monitoring of the Youth Environment (CISM). For international organizations, the mandate is clear: Defense must be as coordinated as the attack. Proactive information sharing between agencies (CISA, NATO, Eurojust, Europol) and private sector defense contractors is the only way to effectively neutralize the impact of these state-sanctioned, high-velocity DDoS campaigns.
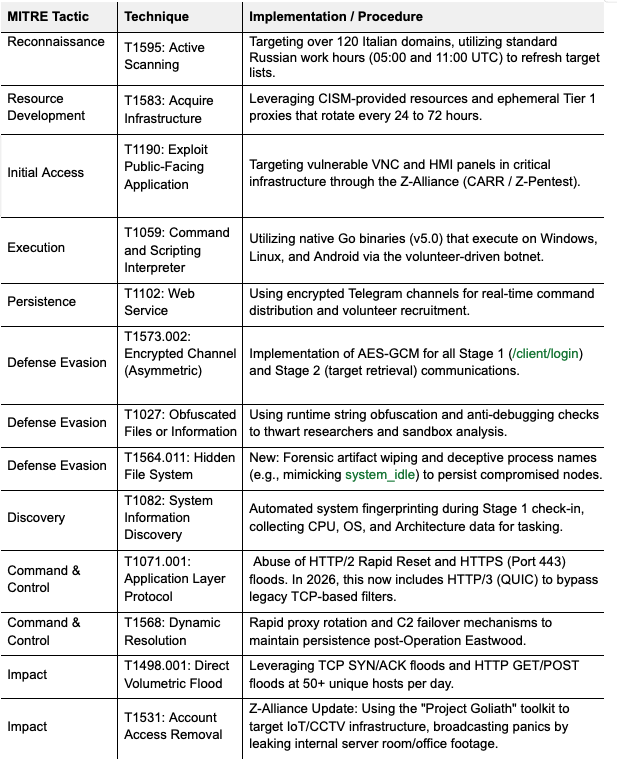
7) Key TTPs
8) References
[1] NoName057(16) and DDoSia Project Analysis: Russia's Most Persistent Hacktivist Operation
[3] Unmasking NoName057(16): Botnets, DDoSia, and NATO
[4] NoName Ransomware Group Targets Transport Organizations in the UK
[5] UK govt. warns about ongoing Russian hacktivist group attacks
[6] NSA, FBI, and Others Call Out Pro-Russia Hacktivist Groups Targeting Critical Infrastructure
Report prepared by Augur Research
For questions or additional analysis, contact: research@augursecurity.com




