Cyber Threat Update: Israel-Iran Conflict & Industry Impact
Date: June 25, 2025
Threat Level: SEVERE
1. Executive Summary - Clear and Present Danger
The cyber conflict between Israel and Iran has intensified into a high-stakes digital battleground, and its scope has now clearly expanded to include direct threats to the United States' critical infrastructure. Critical infrastructure operators in the Middle East and North Africa (MENA) region, particularly in the petroleum sector, continue to face a severe threat. However, recent intelligence and a National Terrorism Advisory System (NTAS) bulletin from the U.S. Department of Homeland Security (DHS) confirm that Iranian state-sponsored and aligned hacktivist groups are actively targeting U.S. networks.
Iranian-aligned advanced persistent threat (APT) groups (including APT34/OilRig, APT35/Charming Kitten, and CyberAv3ngers) are executing credential phishing, exploiting unpatched vulnerabilities, and deploying custom malware to penetrate and destabilize networks in both the MENA region and the United States. The pro-Israel actor Predatory Sparrow continues its highly sophisticated, public-facing operations against Iranian financial and critical infrastructure targets, signaling a deliberate strategy of economic destabilization.
Recent findings also confirm renewed activity by the Iranian group known as BladeFeline. After nearly a decade underground, they're now deploying an expanded malware arsenal designed to evade conventional defenses, including new malware families like Whisper and PrimeCache. For regional petroleum operators, the immediate threat is no longer theoretical. Production disruptions, OT/ICS network breaches, and data theft are all realistic scenarios. For U.S. entities, particularly in the water, energy, and healthcare sectors, the threat of disruptive cyberattacks is now a documented reality.
This report presents the updated threat landscape and actionable steps to secure your infrastructure.
2. Key Takeaways
- Expanded Threat to the U.S.: Pro-Iranian cyber actors are no longer limiting their focus to the MENA region. Recent advisories from CISA, the FBI, and the NSA highlight a direct and growing threat to U.S. critical infrastructure, especially the water and energy sectors.
- OT/ICS Infrastructure is in the Crosshairs: Malware, such as IOCONTROL and PrimeCache, are tailored to target supervisory control and data acquisition (SCADA) and automation systems.
- Destruction is Active, Not Hypothetical: Wipers, data encryption malware, and sabotage scripts are being deployed in live environments.
- Economic Destabilization & Psychological Warfare are Strategic Weapons: Predatory Sparrow’s high-profile hacks (e.g., Nobitex, Bank Sepah) are designed to erode confidence and destabilize Iran’s economy.
- Long-Dwell Threats are Active: BladeFeline’s stealth tactics underscore the risk of deeply embedded threats that evade traditional detection methods.
- Global Spillover is Already Happening: With U.S. and European involvement in regional energy infrastructure, spillover effects are likely and have already been observed.
- DDoS and IoT-Based Flooding Tactics are Intensifying: Iranian-linked actors are actively using large-scale botnets, such as Eleven11bot, to conduct volumetric attacks targeting telecoms, ISPs, and gaming infrastructure across the MENA and Asia regions.
- Strategic Intelligence-Gathering is Escalating: Recent reports indicate that Iranian state-linked actors successfully exfiltrated military and nuclear-related intelligence from Israeli networks, expanding the strategic impact of their cyber campaigns.
3. Threat Assessment & Analysis
3.1 Recent Developments & Attribution
- DHS Issues NTAS Bulletin (June 2025): The Department of Homeland Security has issued a bulletin stating the current "heightened threat environment" makes it likely that "low-level cyber attacks against U.S. networks by pro-Iranian hacktivists are likely, and cyber actors affiliated with the Iranian government may conduct attacks against U.S. networks."
- Truth Social Attacked (June 2025): Following U.S. military action, the pro-Iranian hacktivist group "313 Team" claimed responsibility for a Distributed Denial-of-Service (DDoS) attack that temporarily took down Donald Trump's Truth Social platform. This highlights the willingness of these groups to target high-profile U.S. entities.
- CISA Advisory on Water Sector Threats (June 2025): CISA, the FBI, and the NSA have released a joint advisory (AA24-290A) detailing the threat of Iranian cyber actors to the U.S. water sector. The advisory highlights the potential for cascading failures in other critical sectors like healthcare and energy.
- CyberAv3ngers Target U.S. Infrastructure (Ongoing): The IRGC-affiliated group "CyberAv3ngers" has been identified as a key perpetrator in attacks on U.S. water systems in late 2023 and continues to pose a threat with custom malware such as IOCONTROL.
- Pro-Iranian Hacktivists Active (June 2025): The pro-Iranian hacktivist group Cyber Fattah conducted a data leak operation against the Saudi Games, as part of a broader anti-US, anti-Israel, and anti-Saudi information campaign.
- June 18, 2025: Predatory Sparrow claimed responsibility for draining $81.7 million in digital assets from Iran’s Nobitex exchange. The funds were reportedly “burned” to deny Iranian access.
- June 17, 2025: A destructive cyberattack by the same group shut down core systems at Bank Sepah.
- 2024-2025: Whisper and PrimeCache malware, attributed to BladeFeline, have been used to compromise ICS and disguise lateral movement across segmented networks (WeLiveSecurity, Hunt.io).
- Public Threats: Iranian-aligned hacktivist channels continue issuing calls to target Western-aligned infrastructure. Telegram and Pastebin were used to publish alleged credentials and targeting data. (See pastebin[.]com/ZgXHgX2S)
- Iran Claims Acquisition of Israeli Military Intelligence (June 2025): Iran claims to have obtained thousands of Israeli intelligence materials, including sensitive documents, photos, and videos related to Israel’s nuclear capabilities. These materials were reportedly transferred from within Israel to Iranian territory, indicating a significant data exfiltration operation focused on military and government intelligence. This incident underscores the broader intelligence-gathering capabilities of Iranian-linked actors, which extend beyond critical infrastructure to include sensitive state and military data.
- DDoS Escalation (May–June 2025): Multiple sources report an increase in Iranian-linked DDoS activity. IoT-based botnets, such as Eleven11bot (linked to tens of thousands of devices inside Iran), have launched volumetric attacks against telecoms and gaming infrastructure. Additionally, Iranian hacktivist groups like Dark Storm Team and Vulture have claimed credit for service disruptions across the Indian and MENA telecom sectors. These waves of attacks are designed to cause widespread service disruptions and to overwhelm public-facing infrastructure during periods of heightened geopolitical tension.
3.2 Threat Actor Profiles
A. Iranian-Aligned APT Groups (APT34/OilRig, APT35/Charming Kitten, CyberAv3ngers)
These groups, acting on behalf of or in alignment with the Iranian government, are building infrastructure designed to breach your operations long before your defenses register a signal.
Motivation: Retaliation, espionage, destabilization of rival economies, and projection of power.
Targets: Government, defense, and critical infrastructure, with a known focus on the energy and water sectors in Israel, the U.S., and Gulf states.
TTPs:
- Initial Access: Spear-phishing, password spraying, and exploitation of unpatched vulnerabilities in public-facing appliances (e.g., VPNs, firewalls).
- Malware: Utilization of custom malware like IOCONTROL for OT/ICS environments, ransomware, and destructive wiper malware like the newly discovered “encryption.exe”, which appears to target Israeli systems specifically, but whose components could be repurposed.
- Impact: Data encryption, data destruction, and manipulation of OT/ICS processes to disrupt physical operations.
- DDoS Operations: Use of Mirai-derived IoT botnets (e.g., Eleven11bot) and Domain Name System (DNS) amplification attacks targeting regional telecom and critical infrastructure.
- Strategic Intelligence Targeting: Recent exfiltration of nuclear and state secrets from Israeli systems suggests an expanded focus on military and intelligence collection.
B. Israeli-Aligned Actors (Predatory Sparrow)
While this group’s attacks are focused on Iran, their methods and the potential for escalation pose an indirect risk.
Motivation: Retaliatory and punitive strikes against Iranian state interests.
Targets: Iranian critical infrastructure, financial institutions, and government entities.
TTPs:
- Sophistication: Operations demonstrate a high level of technical skill, resource backing, and intelligence gathering, indicative of state-level capabilities.
- Impact: Widespread service disruption designed to undermine public confidence and inflict economic pain. Their operations are overt and publicly claimed, amplifying their psychological impact.
C. BladeFeline (Iran-aligned APT)
BladeFeline has operated quietly for nearly a decade and has recently expanded its arsenal with malware capable of affecting ICS. They are now deploying Whisper and PrimeCache to move laterally and persist within hardened ICS environments.
Motivation: Covert surveillance, OT disruption, and intelligence gathering.
Targets: Middle Eastern utilities, telecoms, and energy sector firms.
TTPs:
- Malware: Whisper (used for staging and evasion), PrimeCache (for lateral movement and persistence)
- Tradecraft: Covert long-term access, segmentation bypass, targeting of logging and monitoring systems
3.3 Industry-Specific Impact Analysis
The cyber conflict between Israel and Iran carries significant implications for the finance, oil and gas, and telecommunications industries in the United States and the MENA region.
Finance Sector
- United States: Iranian-linked actors have shown interest in disrupting U.S. financial institutions, especially mid-tier banks and fintech platforms. Techniques include DDoS attacks, phishing, and exploitation of third-party platforms. Objectives range from economic disruption to intelligence gathering and fraud, with potential impacts on market confidence and consumer trust.
- MENA Region: Pro-Israel groups like Predatory Sparrow have engaged in offensive cyber operations against Iranian financial infrastructure, notably draining $81.7M in digital assets from Nobitex and attacking Bank Sepah to disrupt banking services and punish military financing. These actions are designed to cause public disillusionment, economic damage, and disruptive retaliation may impact neighboring financial institutions as collateral.
Water & Wastewater Systems (U.S. Focus)
- Iranian actors are probing municipal utilities across the U.S., exploiting weak segmentation and legacy SCADA. Attacks risk water contamination, chemical tampering, and public health crises, as seen in small-utility incidents reported in 2023–2025. The psychological impact of these attacks is often as significant as the operational disruption.
Energy Sector
- United States: The power grid remains a strategic target. Groups like APT33 and MuddyWater conduct reconnaissance and target OT systems to cause cascading outages across sectors. Disruptions could impact emergency services, healthcare, and transportation.
- MENA Region: Iranian-aligned groups such as APT34 (OilRig), APT35 (Charming Kitten), and CyberAv3ngers have actively targeted petroleum operations, using custom malware like IOCONTROL and PrimeCache. Objectives include SCADA sabotage, data theft, and destructive disruptions with tools like encryption.exe. The petroleum sector faces a SEVERE risk level due to its strategic and economic value.
Healthcare Sector (U.S. Focus)
- Iranian campaigns increasingly target U.S. healthcare networks via ransomware, EHR vulnerabilities, and medical IoT exploitation. Recent campaigns in 2024–2025 show attacks that disrupt care, exfiltrate PHI, and cause EHR outages, raising patient safety concerns and regulatory risks.
Telecommunications Sector (MENA Focus)
- The telecom industry in MENA is under sustained threat from Iranian-linked APTs like BladeFeline, who aim to establish long-term access to Middle Eastern telecoms, utilities, and energy firms. Techniques include segmentation bypass, covert persistence, and use of malware such as Whisper and PrimeCache to disable monitoring/logging. Risks include service disruptions, data theft, and telecom infrastructure being used as a pivot to target other critical sectors.
3.4 New and Confirmed IOCs
New and Confirmed IOCs
The list of IOCs will be provided in a separate spreadsheet (Israel-Iran Conflict & Industry Impact.xlsx).
4. DDoS activity in the USA and MENA Regions - Mira/Moobot (Since Jan 2025)
June 2025 saw a sharp increase in blocking activity related to DDoS campaigns, with a peak of 98,239 events blocked in the US and 91,164 in the MENA region. All these events originated from the IP address 109.205.213[.]30, which Augur Security had flagged as malicious on January 29, 2022. This IP belongs to the 109.205.213.0/24 subnet, which exhibits a 100% infection rate, suggesting the entire range is compromised or under adversary control. This specific IP address has been observed targeting large organizations in the USA and MENA's finance and oil & gas sectors.
This IP is historically associated with Mirai botnet operations and was actively scanning for CVE-2023-28771 — a critical remote code execution vulnerability in Zyxel firewall and VPN devices. Exploitation of this flaw enables unauthenticated attackers to send crafted IKE packets to execute OS commands, potentially leading to complete device compromise.
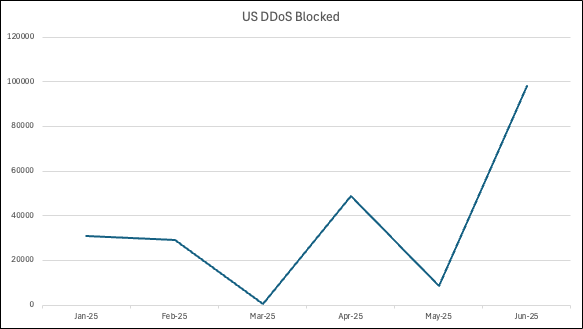
Figure 1. Count of events blocked in the last 6 months related to DDoS malware

Figure 2. Count of events blocked in the last 6 months related to DDoS malware
5. Recommendations
Strategic Recommendations
- Activate Incident Response (IR) Plans: Your IR plan isn’t just about detection anymore; it’s about controlling the blast radius before the detonation. Convene your IR team to review and update plans based on scenarios involving wiper malware and OT/ICS disruption. Conduct a tabletop exercise within the next seven (7) days.
- Enhance Threat Intelligence Posture: Increase the frequency of intelligence updates from trusted sources (e.g., CISA, sector-specific ISACs) and ensure they are effectively operationalized by your Security Operations Center (SOC).
- Review Third-Party Risk: Assess the security posture of partners and suppliers with network access, as they can be used as an entry vector.
Operational & Technical Recommendations
- Patch Aggressively: Immediately patch all internet-facing systems, especially VPNs, firewalls, and remote access solutions. Prioritize vulnerabilities known to be exploited by Iranian APTs.
- Harden OT/ICS Environments:
- Review and enforce network segmentation between IT and OT networks.
- Disable any internet access to OT/ICS devices that are not operationally essential.
- Change all default credentials on Programmable Logic Controllers (PLCs), Human-Machine Interfaces (HMIs), and other OT devices.
- Ensure OT assets are included in your monitoring and incident response visibility.
- Implement IOCs: Task your SOC with proactively hunting for the IOCs listed in this report across your network and endpoints.
- Enforce Multi-Factor Authentication (MFA): Ensure MFA is enabled on all remote access accounts, privileged accounts, and cloud services.
- Enhance Monitoring: Increase logging and monitoring of network traffic, particularly for connections to and from the OT environment, and look for anomalous use of protocols such as MQTT.
- DDoS Preparedness: Deploy DDoS mitigation services (cloud or ISP-based). Establish peering policies with upstream providers and monitor for volumetric and amplification signatures from IoT sources.
- Monitor High-Value Data Exfiltration: Implement data loss prevention (DLP) strategies on sensitive military, R&D, or nuclear-related assets. Tag and monitor sensitive project folders or research repositories to ensure secure access.
- Review and enforce network segmentation between IT and OT networks.
- Disable any internet access to OT/ICS devices that are not operationally essential.
- Change all default credentials on PLCs, HMIs, and other OT devices.
- Ensure OT assets are included in your monitoring and incident response visibility.
For further information or enquiries on the research above, please contact the Augur Threat Research team (research@augursecurity.com)
6. Sources & References
- (Axios, 2025). U.S. braces for Iranian cyberattacks on critical infrastructure. Axios. Retrieved from https://www.axios.com/2025/06/17/us-iran-israel-cyberattacks-critical-infrastructure
- (CNBC, 2025). Pro-Israel hackers say they stole millions from Iran’s largest crypto exchange and ‘burned’ it. CNBC. Retrieved from https://www.cnbc.com/2025/06/18/pro-israel-hackers-iran-crypto.html
- (CISA, n.d.). Iranian Government-Sponsored APT Actors. Cybersecurity & Infrastructure Security Agency. Retrieved from https://www.cisa.gov/topics/cyber-threats-and-advisories/nation-state-cyber-actors
- (Industrial Cyber, 2025). Radware warns of surge in Iranian cyber activity targeting Israeli industrial, critical systems. Industrial Cyber. Retrieved from https://industrialcyber.co/industrial-cyber-attacks/radware-warns-of-surge-in-iranian-cyber-activity-targeting-israeli-industrial-critical-systems/
- (ISW, 2025). Iran Update, June 18, 2025. Institute for the Study of War. Retrieved from https://www.understandingwar.org/backgrounder/iran-update-special-report-june-18-2025-evening-edition
- (Politico, 2025). Iran orders officials to ditch connected devices. Politico. Retrieved from https://www.politico.eu/article/iran-orders-officials-to-ditch-connected-devices/
- (The Record, 2025). Pro-Israel hackers claim breach of Iranian bank amid military escalation. The Record from Recorded Future News. Retrieved from https://therecord.media/pro-israel-hackers-claim-attack-on-iranian-bank
- (WSJ, 2025). Companies Warned to Be on Alert for Iranian Cyberattacks. The Wall Street Journal. Retrieved from https://www.wsj.com/articles/companies-warned-on-iranian-cyberattacks-9902c1d9
- (NY Post, 2025). US businesses warned to brace for Iranian cyberattacks as war with Israel escalates. NY Post. Retrieved from https://nypost.com/2025/06/18/business/us-businesses-warned-to-brace-for-iranian-cyberattacks-amid-war-with-israel/
- (Times of India, 2025). Take immediate action: Researchers warn US companies of Iranian cyberattacks. Times of India. Retrieved from https://timesofindia.indiatimes.com/technology/tech-news/take-immediate-action-to-researchers-warn-us-companies-of-iranian-cyberattacks/articleshow/121938807.cms
- (Cyber_ra1, 2025). Infrastructure IOCs tied to Iranian and Israeli actors. X. Retrieved from https://x.com/cyber_ra1/status/1932310301921394744
- (Nigroeneveld, 2025). Observations of APT35 infrastructure abuse. X. Retrieved from https://x.com/nigroeneveld/status/1917200289817305205
- (Blackorbird, 2025). Commentary on APT activity evolution. X. Retrieved from https://x.com/blackorbird/status/1899462139984925136
- (Pastebin, 2025). Exposed credentials allegedly tied to Iranian targets. Pastebin. Retrieved from https://pastebin.com/ZgXHgX2S
- (Weixin, 2025). Summary of regional threat actor activity. WeChat. Retrieved from https://mp.weixin.qq.com/s/nY2Hyg6ZsM7ViXW1lhO2Ag
- (Abuse.ch, 2025). Malware samples associated with APT35. Abuse.ch Malware Bazaar. Retrieved from https://bazaar.abuse.ch/browse/tag/APT35/
- (Abuse.ch, 2025). Malware samples associated with APT34. Abuse.ch Malware Bazaar. Retrieved from https://bazaar.abuse.ch/browse/tag/APT34/
- (Unit42, 2025). Iranian attackers impersonate model agency for phishing. Unit 42. Retrieved from https://unit42.paloaltonetworks.com/iranian-attackers-impersonate-model-agency/
- (Fortinet, 2025). Middle East incident response trends. Fortinet. Retrieved from https://www.fortinet.com/content/dam/fortinet/assets/reports/report-incident-response-middle-east.pdf
- (Hunt.io, 2025). Infrastructure tracking of APT34-like campaigns. Hunt.io. Retrieved from https://hunt.io/blog/track-apt34-like-infrastructure-before-it-strikes
- (DarkReading, 2025). Iranian APT BladeFeline operated covertly for 8 years. DarkReading. Retrieved from https://www.darkreading.com/threat-intelligence/iranian-apt-bladedfeline-hides-network-8-years
- (Security Online, 2025). BladeFeline expands with Whisper and PrimeCache malware. SecurityOnline.info. Retrieved from https://securityonline.info/bladedfeline-iran-aligned-apt-group-expands-arsenal-with-whisper-and-primecache/
- (ESET, 2025). BladeFeline’s WhisperingDark campaign analyzed. WeLiveSecurity. Retrieved from https://www.welivesecurity.com/en/eset-research/bladedfeline-whispering-dark/
- (DigitalBank, 2025). Technical breakdown of U.S.-Iran cyber escalation. DigitalBank Capital. Retrieved from https://www.digitalbank.capital/post/cyber-warfare-between-the-u-s-and-iran-a-technical-deep-dive-into-tools-tactics-and-escalating-t




