Q1 was a big quarter for the Augur development team, delivering a wave of powerful new features and enhancements. From the new Bulletproof Hoster feed and Brand Safety module to our Cicero AI threat research assistant, this release is designed to add deeper context and enrichment to our predictive threat intelligence. The result is a more usable, more actionable platform that strengthens Augur’s position as the most impactful preemptive cybersecurity solution on the market.
Here are some of the highlights from Q1:
Bulletproof Hosting Label & Feed: New label and bulk feed exposing known bulletproof hosting providers, enabling automated ingestion into blocking and enrichment pipelines.
Being able to identify bulletproof hosters provides critical context for IOC analysis by highlighting infrastructure that is deliberately resistant to takedown and commonly associated with sustained malicious operations. It shifts the focus from simply validating an indicator to understanding the resilience and intent behind the supporting infrastructure. When an IOC is tied to a known bulletproof hoster, it increases confidence in its maliciousness, signals a higher likelihood of reuse or persistence, and helps prioritize investigation and response.

VPN and Residential Proxy Detection: IP enrichment now flags residential proxy usage, surfaced inline on IP detail pages.
VPN and residential proxy detection is becoming more and more critical as attackers increasingly use these methods to evade IP reputation systems and blend in with legitimate user traffic. It shifts the focus from what infrastructure attackers will use to how attackers access and operate through that infrastructure. This makes it possible to flag when logins, outbound connections, or API calls originate from residential proxies or anonymization services commonly used by attackers, helping identify account takeover attempts, initial access activity, and lateral movement disguised as normal traffic.

Credential Exposure Module: This new module surfaces compromised credential data tied to your organization and assets.
Compromised, leaked, and stolen credentials remain one of the most reliable and scalable entry points for attackers. Surfacing exposed usernames, passwords, tokens, or session data shifts the focus from detecting intrusion attempts to identifying access that may already be available to threat actors. This provides early visibility into potential account takeover, privilege escalation, and lateral movement risks, while enabling faster remediation through credential resets, access reviews, and stronger authentication controls. The result is reduced dwell time and a more limited overall impact.
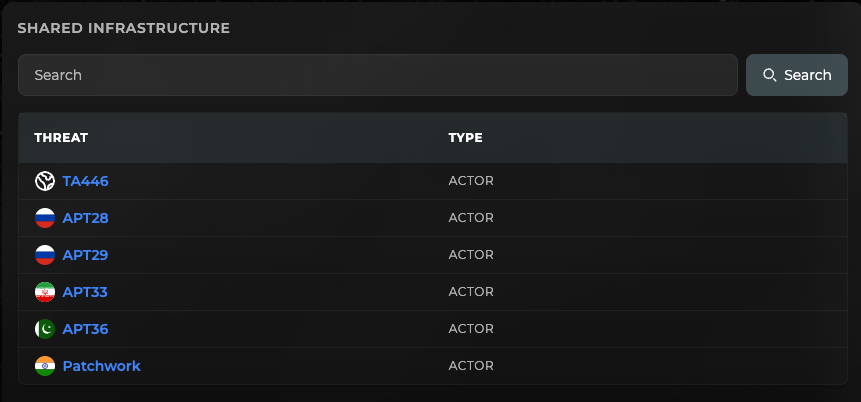
Shared Infrastructure View: We’ve also created a new dedicated view to explore infrastructure overlap across threat actors, surfacing shared resources with country attribution and sponsoring organizations for geopolitical context.
The Shared Infrastructure View helps reveal connections that are often missed when analyzing campaigns in isolation. Adding country attribution and context on the sponsoring organization moves the analysis beyond technical indicators to include geopolitical intent and alignment. This enables faster pivoting, stronger attribution hypotheses, and a clearer understanding of how different actors may be linked, coordinated, or reusing infrastructure at scale.
Cicero AI Assistant: Our first user-facing AI feature, the Cicero AI Conversational AI widget, allows users to query IOCs, infrastructure, and threat context directly from the platform without leaving their workflow.
With Cicero, analysts can rapidly validate indicators, enrich findings, and explore relationships, instead of spending time pivoting between tools or manually querying datasets. Cicero helps analysts surface insights faster, allowing teams to move from data to decision with confidence.

Also Launched Last Quarter
Feed ROI Dashboard: A unified scoring view lets analysts evaluate and filter feed performance by category, with confidence scores for each feed to prioritize intelligence sources and guide investment decisions.
CrowdStrike SIEM Integration: Native event feedback parser for CrowdStrike SIEM with guided setup documentation and integration assets included.
AWS VPC Netflow: Improved concurrent stream processing for AWS VPC integrations, reducing ingestion latency at scale.
Incoming / Outgoing Event Toggle: Switch between inbound and outbound event perspectives on any monitored asset.
We also pushed out a long list of behind-the-scenes platform and API enhancements to enhance day-to-day usability and dependability.
Coming In Q2
PDF Threat Report Ingestion: Upload third-party threat reports in PDF format for automated IOC extraction and correlation against Augur data.
Stay up to date on all the latest from Augur by following us on LinkedIn


.png)

